📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 244 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (10481)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
14h ago
BankGPT | TryHackMe Writeup
TryHackMe | BankGPT Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
14h ago
You May Have Perfect Backups and Still Lose Everything
Backup Best Practices for Data You Cannot Afford to Lose Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
14h ago
Malloc Privacy Weekly
We bring you the most recent mobile cybersecurity updates in the newest edition of Malloc Weekly Privacy. This week, we cover the surge in… Continue reading on
Medium · Cybersecurity
14h ago
IDS vs IPS:Intrusion Detection vs Prevention Systems
CORE IDEA Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
14h ago
Bug Bounty Hunting — Ethical Hacking for Profit
What if hacking could be legal, respected, and even highly profitable? Continue reading on Medium »
Medium · Cybersecurity
🧠 Large Language Models
⚡ AI Lesson
14h ago
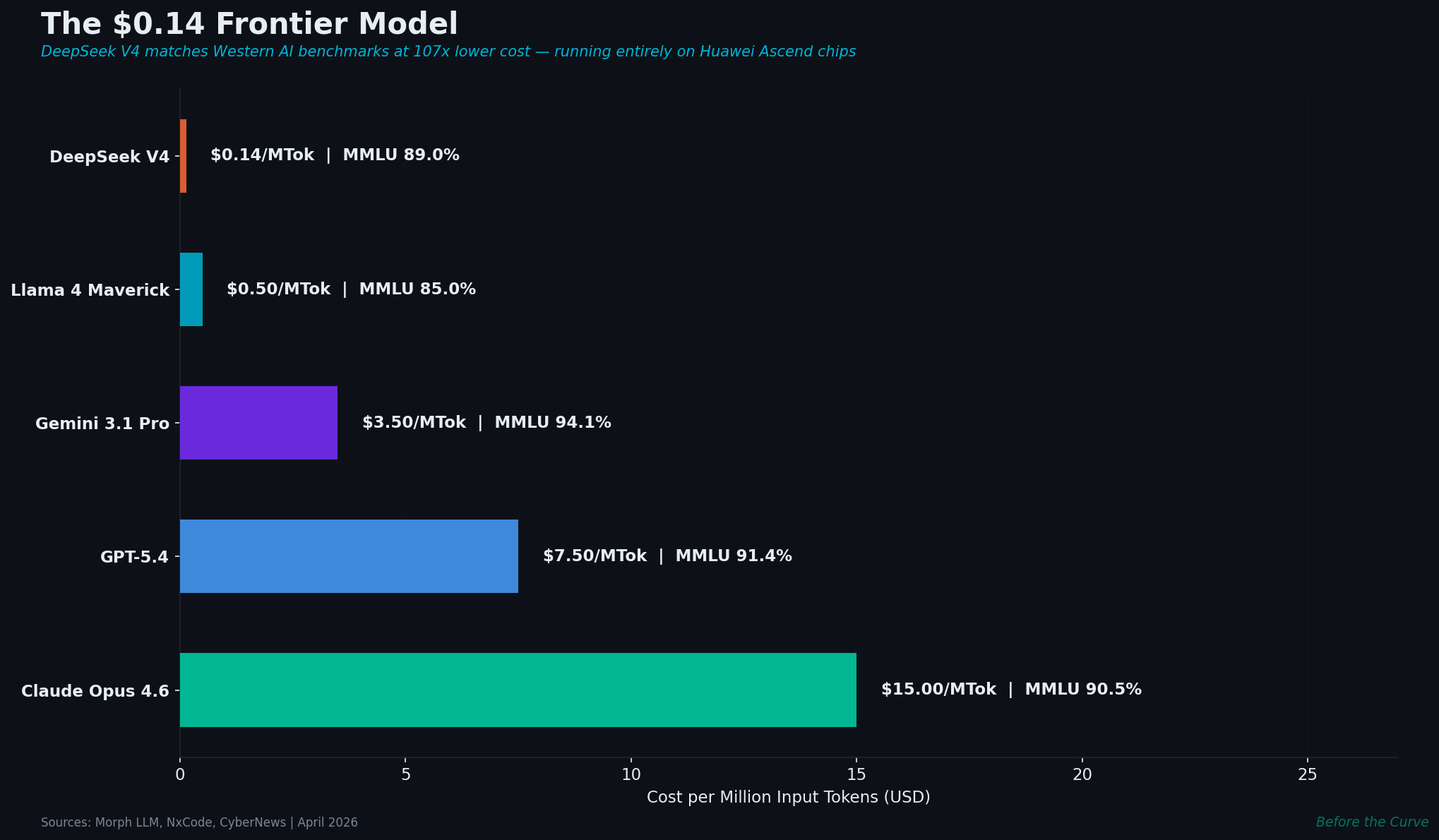
DeepSeek V4: 1 Trillion Parameters, $0.14/M Tokens, No NVIDIA
China’s latest frontier model costs 107× less than Western alternatives and runs entirely on Huawei chips. With 175,000 open-source AI… Continue reading on Medi

Medium · Cybersecurity
14h ago
How Raw Alerts Become Analyst-Ready Jira Tickets — Automatically | SOC Project — Phase 4
While there are many open-source case management platforms, many enterprises use Jira for tracking security incidents. For this lab, we… Continue reading on Med
Medium · Cybersecurity
15h ago
I Automated My Entire Tier-1 Alert Pipeline With n8n and Gemini | SOC Project — Phase 3
In this phase, we will deploy n8n to handle our security orchestration and automated response (SOAR) workflows. Continue reading on Medium »

Medium · Cybersecurity
📰 AI News & Updates
⚡ AI Lesson
16h ago
Do AI Impact ASIA Company? A 2026 Macroeconomic Technical Audit
The year 2026 marks a decisive pivot point for the Asian corporate landscape. As the “Digital Silk Road” matures, the integration of… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
16h ago
The 2026 Guide to Web Integrity: Understanding the Role of SSL in Modern App Ecosystems
In the current digital landscape of 2026, the internet is no longer a luxury; it is the backbone of global commerce and entertainment… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
16h ago
Attackers don’t hack systems — they hack decisions
The real vulnerability isn’t your software. It’s the three seconds before you click. Continue reading on Medium »

Medium · Cybersecurity
16h ago
Authentication Bypass — How Attackers Become Anyone
✍️ Introduction Continue reading on Bug Bounty Hunting: A Comprehensive Guide in English and french »

Medium · Cybersecurity
16h ago
SOC Automation Lab Series 3
Now since we have our Wazuh and TheHive ready letsconfigure our wazuh to windows 11 agent Continue reading on Medium »

Medium · Cybersecurity
16h ago
Cybersecurity 2026: Resilience, AI Governance, and the Global Challenge
From fintech ransomware to global compliance, lessons in resilience and trust. Continue reading on Medium »

Medium · Cybersecurity
16h ago
This Week in Tech: Unpatched, Unleashed, and Unstoppable
TL;DR Continue reading on Medium »

Medium · Cybersecurity
17h ago
Monitoring DNS Traffic for Suspicious Activity using Wireshark
The goal was to isolate DNS traffic and capture packets for analysis. Continue reading on Medium »

Medium · Cybersecurity
17h ago
My Bug Bounty Journey #10: Start Your Bug Bounty Journey Today
The End Continue reading on Medium »

Medium · Cybersecurity
18h ago
Verification Without Exposure: Proving Without Revealing
Introduction Continue reading on Medium »

Medium · Cybersecurity
18h ago
Trust Is Not a State: It’s a Continuous Verification Process
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
18h ago
What Scale-Up CISOs Actually Need: The Politics Nobody Prepares You For
The Scale-Up CISO series by John Rouffas Continue reading on Medium »
Medium · Cybersecurity
18h ago
⚙️ 09. — Insecure Direct Object References (IDOR)
Continue reading on Medium »
Medium · Cybersecurity
18h ago
⚙️ 08. — User ID controlled by request parameter with password disclosure
Continue reading on Medium »

Medium · Cybersecurity
18h ago
Investigating Windows Event Logs: A Practical Digital Forensics Walkthrough
Introduction Continue reading on Medium »

Medium · Cybersecurity
19h ago
FortiGate Dashboard (Status) Ekranı: Temel Bileşenlerin İncelenmesi
Genel Bakış Continue reading on Medium »
 DeepCamp AI
DeepCamp AI