📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 254 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (10574)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
9h ago
AI Cyber Shockwave: Claude Mythos Triggers Urgent UK Security Response
The emergence of AI cybersecurity threats, AI-driven cyber attacks, Claude Mythos, AI security risks, penetration testing, cybersecurity… Continue reading on Me
Medium · Cybersecurity
9h ago
Why I’m Joining the “Barstool Vulnerability Experts” on Project Glasswing
If you’ve been on LinkedIn or read the news this week, you’ve seen the headlines. Anthropic’s Claude Mythos and Project Glasswing have… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
11h ago
Why CISSP Is the Most Valuable Cybersecurity Certification for Senior Professionals in 2026
The cybersecurity landscape has never been more competitive — or more rewarding — for those who hold the right credentials. Among the… Continue reading on Mediu

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
11h ago
5 Ways AI Agents Are Automating Cybersecurity in US Enterprises for 2025
In 2025, Artificial Intelligence (AI) Agents are transforming how US enterprises defend against cyber threats by automating and enhancing… Continue reading on M
Medium · Cybersecurity
11h ago
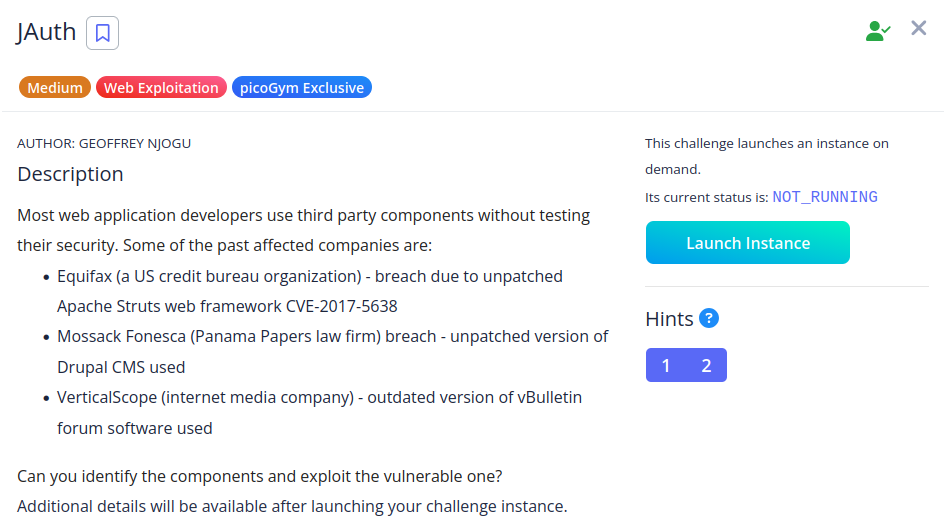
Writeup for picoCTF challenge “JAuth”
Manipulate a JWT authentication token to escalate privileges and learn why the “none” algorithm should rarely be used Continue reading on Medium »
Medium · Cybersecurity
11h ago
Process Injection Techniques
Introduction : Continue reading on Medium »

Medium · Cybersecurity
11h ago
Cybersecurity in Transportation Systems
Explore cybersecurity in transportation systems, key risks, real-world threats, and strategies to secure modern mobility infrastructure… Continue reading on Med

Medium · Cybersecurity
11h ago
The Registry Analyst’s Toolkit: Choosing Your Weapon
Every craftsman will tell you the same thing — knowing your tools is half the battle. You could understand the Windows Registry inside and… Continue reading on

Medium · Cybersecurity
12h ago
Web Application Security Summer Training Internship in Delhi NCR
Introduction: Continue reading on Medium »

Medium · Cybersecurity
12h ago
Staying Safe on Fiverr: My Personal Encounter with Scammers and How to Protect Your Account.
Introduction Continue reading on Medium »

Medium · Cybersecurity
12h ago
The Hidden Liability of “Free” Software: A Framework for Open Source Due Diligence
Open-source software (OSS) is the backbone of modern enterprise infrastructure, yet most organizations adopt it without a formal risk… Continue reading on Mediu

Medium · Cybersecurity
12h ago
What 27 Years of Missed Bugs Tells Us About Human Cognition
The OpenBSD vulnerability wasn’t hidden. It was in plain sight. That distinction matters more than the cybersecurity industry has… Continue reading on Medium »

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
13h ago
AI Agents and the End of Deterministic Cybersecurity
From API workflow abuse to autonomous decision chains — the new security paradigm emerging around AI agents. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
13h ago
The Cybersecurity Gap No One Is Talking About: Claude Mythos vs Opus 4.6
Most people think AI in cybersecurity is just getting better. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
13h ago
Tek Bir Link ile Uygulamayı Ele Geçirmek: Deep Link ve WebView İstismarı
Mobil Dünyanın Arka Kapıları: WebView ve DeepLink Zafiyetleri Continue reading on Medium »

Medium · Cybersecurity
13h ago
CyberDefenders — WebStrike Writeup
Scenario: Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
13h ago
Why shared responsibility models confuse SMEs.
Shared responsibility looks clean in a diagram. Continue reading on aneo Security Insights »

Medium · Cybersecurity
13h ago
Transition from IPv4 Exhaustion to IPv6: The Future of the Internet
The rapid exhaustion of IPv4 addresses, which form the foundation of the internet, makes the transition to a new generation protocol, IPv6… Continue reading on

Medium · Cybersecurity
13h ago
FBI Atlanta and Indonesian National Police Take Down W3LLSTORE Phishing Marketplace
Continue reading on Medium »

Medium · Cybersecurity
13h ago
GRC vs. IT Operations: Why the ISO Must Be a Bridge Builder
Bridging the gap between the 2nd and 1st Line through eye-level collaboration and common-sense pragmatism. Continue reading on Medium »

Medium · Cybersecurity
14h ago
Why I’m Building a Cyber Intelligence Project From Scratch — And What’s Coming.
This is day one. Here’s everything. Continue reading on Medium »

Medium · Cybersecurity
14h ago
Inside a Web Shell Attack: TryHackMe First Shift CTF — Task 5: Portal Drop
A SOC Threat Intelligence Investigation into Brute Force, File Upload Exploitation, and Web Shell Persistence Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
15h ago
Is your security strategy reactive — or intelligently proactive?
易 Zefai Insights || Cyber Security Edition Continue reading on Medium »
Medium · Cybersecurity
🧠 Large Language Models
⚡ AI Lesson
15h ago
LLM Injection + Unlimited Approval + RCE: The Coinbase AgentKit Attack Chain
A prompt injection that crosses three trust boundaries — and why Coinbase called it Medium Continue reading on Medium »
 DeepCamp AI
DeepCamp AI