📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 164 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (10081)
ArXiv cs.AIDev.to · FORUM WEBForbes InnovationDev.to AIOpenAI NewsHugging Face Blog
Medium · Cybersecurity
5h ago
Virtual Hosts: Discovering Hidden Web Applications Beyond DNS
Introduction Continue reading on Medium »

Medium · Cybersecurity
5h ago
Practical Vulnerability Analysis with Nessus on a Metasploitable System
1. Project Overview Continue reading on Medium »
Medium · Cybersecurity
5h ago
DNS Zone Transfers: The Silent Information Leak in DNS by Mert Baykal
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5h ago
Reverse Engineering on CyberTalents: Solving All Easy Challenges Part 2
Challenge 3: “Pure Luck” Reverse Engineering Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6h ago
How I Bypassed Premium Subscription & Escalated Privileges Using a $0 VCC (Business Logic Flaw)
Introduction : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6h ago
Before MYTHOS Ships, Someone Has to Fix the World
An Op-Ed on Anthropic’s Ethical Bind Continue reading on Medium »

Medium · Cybersecurity
🔢 Mathematical Foundations
⚡ AI Lesson
6h ago
Beyond the Number Line From Integers to Infrastructure Completing Chapter 1 of the Math-to-Code…
“I am proud to announce the completion of the first major chapter in my technical journey: Numbers and Negative Numbers From Krista King’s… Continue reading on
Medium · Cybersecurity
6h ago
Finding Flags in SVG/XML Files — A Beginner Forensics Approach
SVG files are often underestimated in CTF forensics. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
7h ago
Anthropic’s New AI Found Bugs in Every Major OS and Browser — And They’re Not Releasing It
Claude Mythos Preview just found thousands of zero-day vulnerabilities. Apple, Google, Microsoft, and AWS are already using it. You can’t. Continue reading on L
Medium · Cybersecurity
7h ago
Slopaganda: What Generative AI Has Done to the Economics of Lying
It used to cost money, time, and skilled operators to run a disinformation campaign at strategic scale. Generative AI has made convincing… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
7h ago
Windows Defender Killer: Combining Registry Edits with BYOVD for Permanent Disable
In the latest update to the Windows Defender Killer repository, I added a powerful new component: a BYOVD (Bring Your Own Vulnerable… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
7h ago
Using AI Without Fundamentals Is the Fastest Way to Stay a Beginner
You can look like you’re learning cyber security without actually learning anything. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
7h ago
Lab Ortamında FortiGate Kurulumu: Adım Adım Rehber
Bu yazıda lab ortamında FortiGate firewall kurulumu adım adım anlatılacaktır. Siber güvenlik alanına ilgi duyanlar ve özellikle SOC… Continue reading on Medium

Medium · Cybersecurity
8h ago
CYBERDUDEBIVASH® PRIVATE LIMITED — OFFICIAL WORKPLACE, GST & PAN VERIFIED GLOBAL CYBERSECURITY…
Daily Threat Intel by CyberDudeBivash Zero-days, exploit breakdowns, IOCs, detection rules & mitigation playbooks. Continue reading on Medium »

Medium · Cybersecurity
8h ago
Chain Reaction Walkthrough Notes | TryHackMe
Axios attack shows risks of unsafe dependencies in development Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
8h ago
How APTs Breach, Persist, and Devastate Networks
Advanced persistent threats (APTs) are well-funded, evasive, and determined to penetrate networks containing sensitive… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
Digital Evidence is Dead.
Why AI watermarks and warning labels are a losing battle against physics and human psychology Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
Beyond the CLI: Reimagining Network Recon with Cyber-Eye Mapper v4.0
The power of Nmap, the elegance of a modern web dashboard, and the security of AES-256 encryption — all in one orchestration layer. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
Post-Exploitation Pivoting in a Lab Environment Using Meterpreter
Internal Network Enumeration and Service Access Through a Compromised Linux Host Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
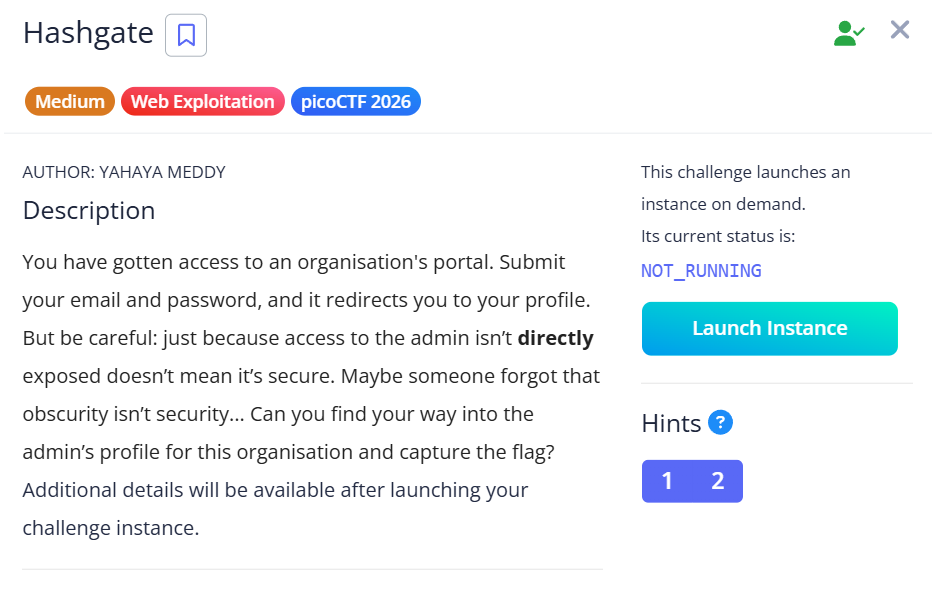
HashGate — picoCTF 2026 Writeup
Category: Web Exploitation | Difficulty: Medium Continue reading on Medium »
Medium · Cybersecurity
🛡️ AI Safety & Ethics
⚡ AI Lesson
9h ago
Why CIOs and CISOs Block AI and What AI Vendors Miss
AI adoption is accelerating across the enterprise. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
Break-Glass Accounts in 2026
Why Passwordless Is No Longer Optional Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
10h ago
Broken Access Control via Replay Attack
How a simple replay trick bypasses permission checks on a popular project management platform Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
10h ago
Obsession Writeup Español
La máquina Obsession se encuentra en la plataforma de Dockerlabs, creada por “El Pingüino de Mario” esta máquina está catalogada como “MUY… Continue reading on
 DeepCamp AI
DeepCamp AI