📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 134 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (11332)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Using AI Without Fundamentals Is the Fastest Way to Stay a Beginner
You can look like you’re learning cyber security without actually learning anything. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Lab Ortamında FortiGate Kurulumu: Adım Adım Rehber
Bu yazıda lab ortamında FortiGate firewall kurulumu adım adım anlatılacaktır. Siber güvenlik alanına ilgi duyanlar ve özellikle SOC… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
How APTs Breach, Persist, and Devastate Networks
Advanced persistent threats (APTs) are well-funded, evasive, and determined to penetrate networks containing sensitive… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Digital Evidence is Dead.
Why AI watermarks and warning labels are a losing battle against physics and human psychology Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Beyond the CLI: Reimagining Network Recon with Cyber-Eye Mapper v4.0
The power of Nmap, the elegance of a modern web dashboard, and the security of AES-256 encryption — all in one orchestration layer. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Post-Exploitation Pivoting in a Lab Environment Using Meterpreter
Internal Network Enumeration and Service Access Through a Compromised Linux Host Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
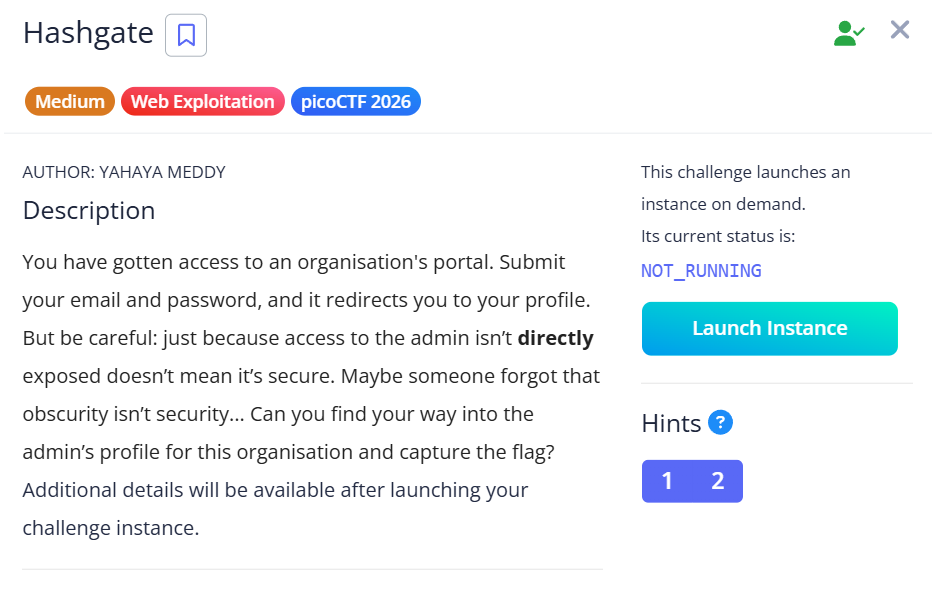
HashGate — picoCTF 2026 Writeup
Category: Web Exploitation | Difficulty: Medium Continue reading on Medium »
Medium · Cybersecurity
🛡️ AI Safety & Ethics
⚡ AI Lesson
2d ago
Why CIOs and CISOs Block AI and What AI Vendors Miss
AI adoption is accelerating across the enterprise. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Break-Glass Accounts in 2026
Why Passwordless Is No Longer Optional Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Broken Access Control via Replay Attack
How a simple replay trick bypasses permission checks on a popular project management platform Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Obsession Writeup Español
La máquina Obsession se encuentra en la plataforma de Dockerlabs, creada por “El Pingüino de Mario” esta máquina está catalogada como “MUY… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Integrating VirusTotal Malware Intelligence with Wazuh — File, IP & URL Scanning
Imagine a new file appears on your system, or your machine suddenly connects to a suspicious IP address — and within seconds, you get an… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
BrowserMon Appliance Released: Enterprise Browser Security, Hardened and Ready to Deploy
A CIS Level 1 hardened OVA that ships pre-configured, pre-loaded, and ready for production Continue reading on Medium »

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
2d ago
You Won’t Believe This Open-Source AI Remembers Your Entire Work Life
Most AI tools answer questions. Rowboat tries to remember your work, organize it into a living knowledge graph, and then act on it. That… Continue reading on Co
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
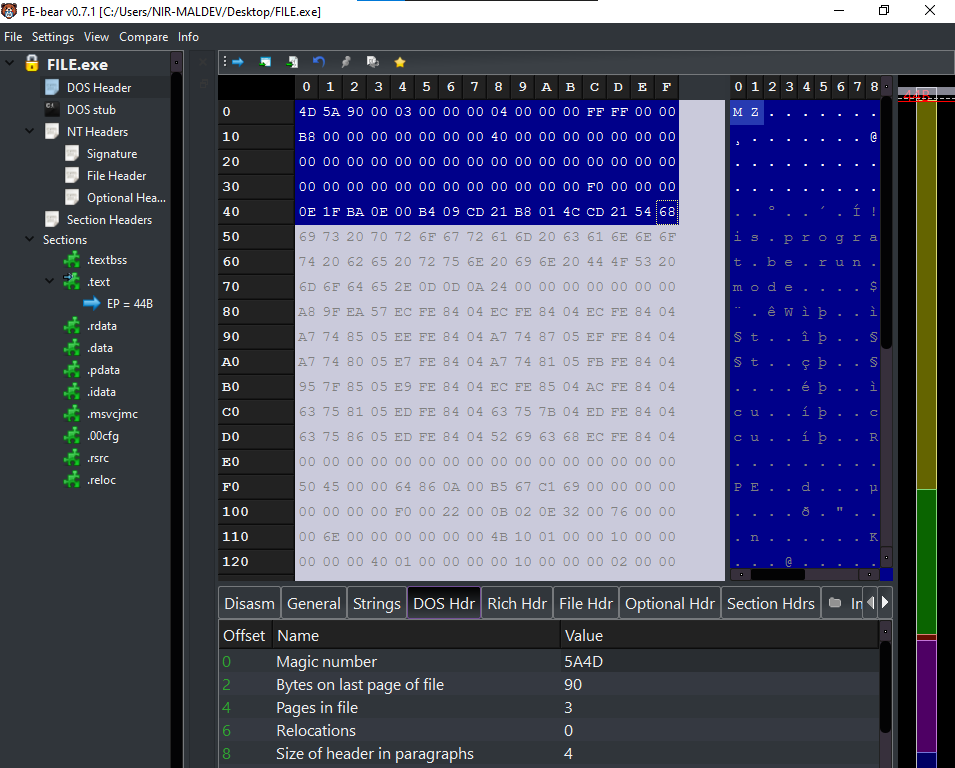
Introduction to DOS Header and DOS Stub (PE)- Nir(7)
Hello, Cybersecurity enthusiasts and white hat hackers!! Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
An AI Model Just Found a 27-Year-Old Zero-Day in OpenBSD
Anthropic’s Claude Mythos — still unreleased, currently gated to about 50 partner orgs through Project Glasswing — autonomously discovered… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Cybersecurity for Scammers
While trying to make a hotel reservation, I unexpectedly found myself in the middle of a critical security vulnerability. In this article… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Forget Hallucination: What if AI Deceives You?
Threads & Perspectives: On Mythos, Statistics, and a Very old playbook Continue reading on Medium »
Medium · Cybersecurity
⚡ AI Lesson
2d ago
Why Your Browser Is Already a Supercomputer (And Why You’re Renting Inferior Clouds)
The shift from server-side processing to client-side WebAssembly is reshaping how professionals handle sensitive data — and most haven’t… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Mr Robot VulnHubWalkthrough | 06/100
Introduction: The Machine That Started With a Smirk Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Analyse des risques stratégiques liés à l’intégration de l’EUDI wallet dans la gouvernance cyber…
La révolution silencieuse de l’EUDI Wallet : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
SOC-Challenge-Day0
Episode 0: Membangun Lab SOC di Cloud Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Phishing Email Analysis SOC Analyst Guide Part-4 Email Authentication.
In this article we are going to touch our created lab a bit to understand the email security checks. Email security is used to protect… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Inside the Rockstar Games Breach: How ShinyHunters Exploited a Hidden Third-Party Weakness
A real-world breach that proves attackers don’t break in, they exploit trust. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI