📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 166 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (11703)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Cybersecurity for Scammers
While trying to make a hotel reservation, I unexpectedly found myself in the middle of a critical security vulnerability. In this article… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Forget Hallucination: What if AI Deceives You?
Threads & Perspectives: On Mythos, Statistics, and a Very old playbook Continue reading on Medium »
Medium · Cybersecurity
⚡ AI Lesson
3d ago
Why Your Browser Is Already a Supercomputer (And Why You’re Renting Inferior Clouds)
The shift from server-side processing to client-side WebAssembly is reshaping how professionals handle sensitive data — and most haven’t… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Mr Robot VulnHubWalkthrough | 06/100
Introduction: The Machine That Started With a Smirk Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Analyse des risques stratégiques liés à l’intégration de l’EUDI wallet dans la gouvernance cyber…
La révolution silencieuse de l’EUDI Wallet : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
SOC-Challenge-Day0
Episode 0: Membangun Lab SOC di Cloud Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Phishing Email Analysis SOC Analyst Guide Part-4 Email Authentication.
In this article we are going to touch our created lab a bit to understand the email security checks. Email security is used to protect… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Inside the Rockstar Games Breach: How ShinyHunters Exploited a Hidden Third-Party Weakness
A real-world breach that proves attackers don’t break in, they exploit trust. Continue reading on Medium »

Medium · Cybersecurity
⚡ AI Lesson
3d ago
45 days Python training summer internship with practical training
A 45 Days Python Training Summer Internship with Practical Training is one of the best ways to start your journey in programming and… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Claude Mythos Might Break Cybersecurity. But Not in the Way You Think.
I’ll be honest with you. When I first read about Claude Mythos, my reaction wasn’t awe. It was a question I couldn’t shake. Continue reading on Medium »

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
3d ago
Weak Gates and High Stakes — My AI Agent gets me on the phone when it needs me!
How I gave my home AI agent a bio-metric approval gate for dangerous commands Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
The scariest AI story of the year!
Big claim, but meet Mythos the AI superhacker breaking bulletproof code. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Building a Windows Server Lab: From Zero to Active Directory Domain Services
Documentation is a key part of the learning process in cybersecurity. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
The Quantum Clock is Ticking: Why the Timeline to Post-Quantum Cryptography Just Crashed
The traditional security paradigm relies on a comforting, yet increasingly dangerous assumption: that a quantum computer capable of… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
The Critical Role of Network Security in the Modern Digital Era
Author: Cera Charles Edward Institution: University of Martland Global Year: 2026 Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
SecurityMetrics Uncovers a 700 Site Global Skimming Operation
SecurityMetrics forensic experts identified a 700 site skimming operation using a sophisticated, multi-channel kit designed to lock out… Continue reading on Cod

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Cyber 101: Living Online: Understanding the Cyber World Without Getting Burned
Imagine we’re just having a casual conversation, trying to make sense of this whole “cyber world” without making it feel like a lecture… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Top 10 Critical CVEs from March 2026 — With Learning Resources & Practical Analysis
Analysis of 10 critical CVEs from March 2026 with practical insights for bug bounty and vulnerability research Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
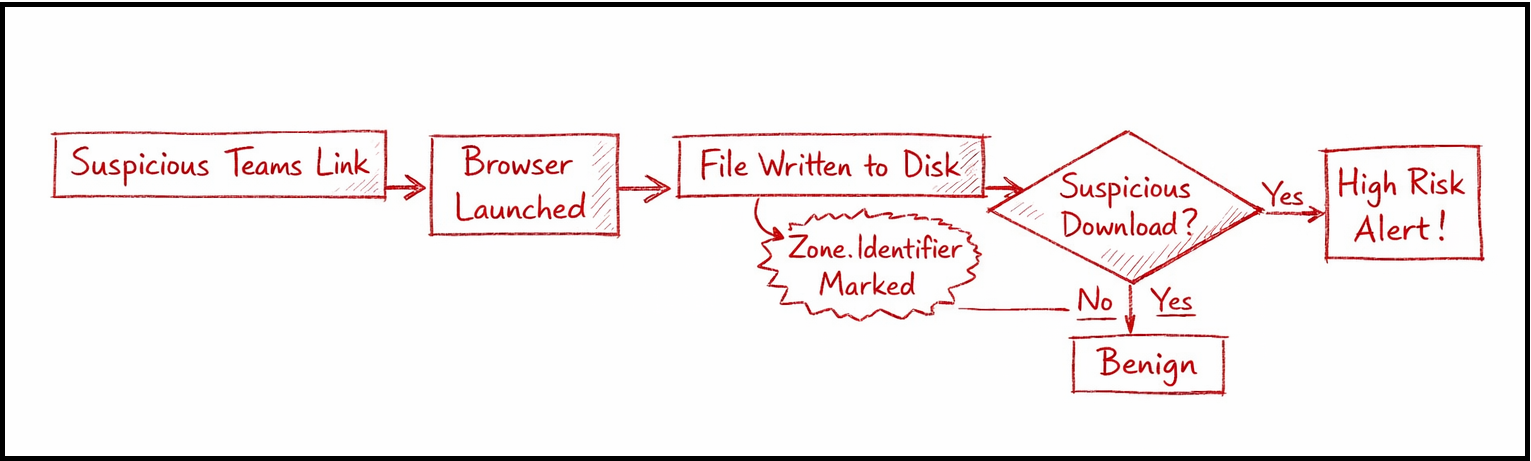
Hunting Malicious Links Delivered via Microsoft Teams: An Endpoint + Cloud Correlation Approach
Modern enterprise attacks are quietly shifting away from traditional entry points like phishing emails. Instead, adversaries are… Continue reading on Medium »

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
3d ago
Built an AI C2 Framework That Plans Attacks Like a Chess Engine.
3 AM. I’m watching an AI agent plan its next move against a lab network. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
WHEN "NOT A VULNERABILITY" GETS PATCHED IN 72 HOURS
By Ahmed Batayneh | March 2026
I submitted 34…
A data-driven analysis of vulnerability coordination patterns in enterprise bug bounty programs. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
PicoCTF Wrieup — Time Machine
Hello everyone, today I will be providing a writeup on the picoCTF problem Time Machine. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
LetsDefend: SOC335 — CVE-2024–49138 Exploitation Detected
How I Investigated CVE-2024–49138 on LetsDefend and What the Artifacts Were Actually Telling Me Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
SOC173 — Follina 0-Day Detected
First we need to understand that why the alert was triggered. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI