📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 126 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (10993)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
The 2026 Guide to Web Integrity: Understanding the Role of SSL in Modern App Ecosystems
In the current digital landscape of 2026, the internet is no longer a luxury; it is the backbone of global commerce and entertainment… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Attackers don’t hack systems — they hack decisions
The real vulnerability isn’t your software. It’s the three seconds before you click. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
What Scale-Up CISOs Actually Need: The Politics Nobody Prepares You For
The Scale-Up CISO series by John Rouffas Continue reading on Medium »

Medium · Cybersecurity
📣 Digital Marketing & Growth
⚡ AI Lesson
1d ago
My Medium Partner Program Suddenly Turned “Inactive” And I Still Don’t Know Why
My Medium Partner Program Turned Inactive — Even After Following All Rules Continue reading on OSINT Team »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
I Found a Broken Login System in a Fintech App — Here’s How I Did It
A real bug hunt story with JWT tokens, Burp Suite, and a fintech website that trusted too much Continue reading on OSINT Team »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
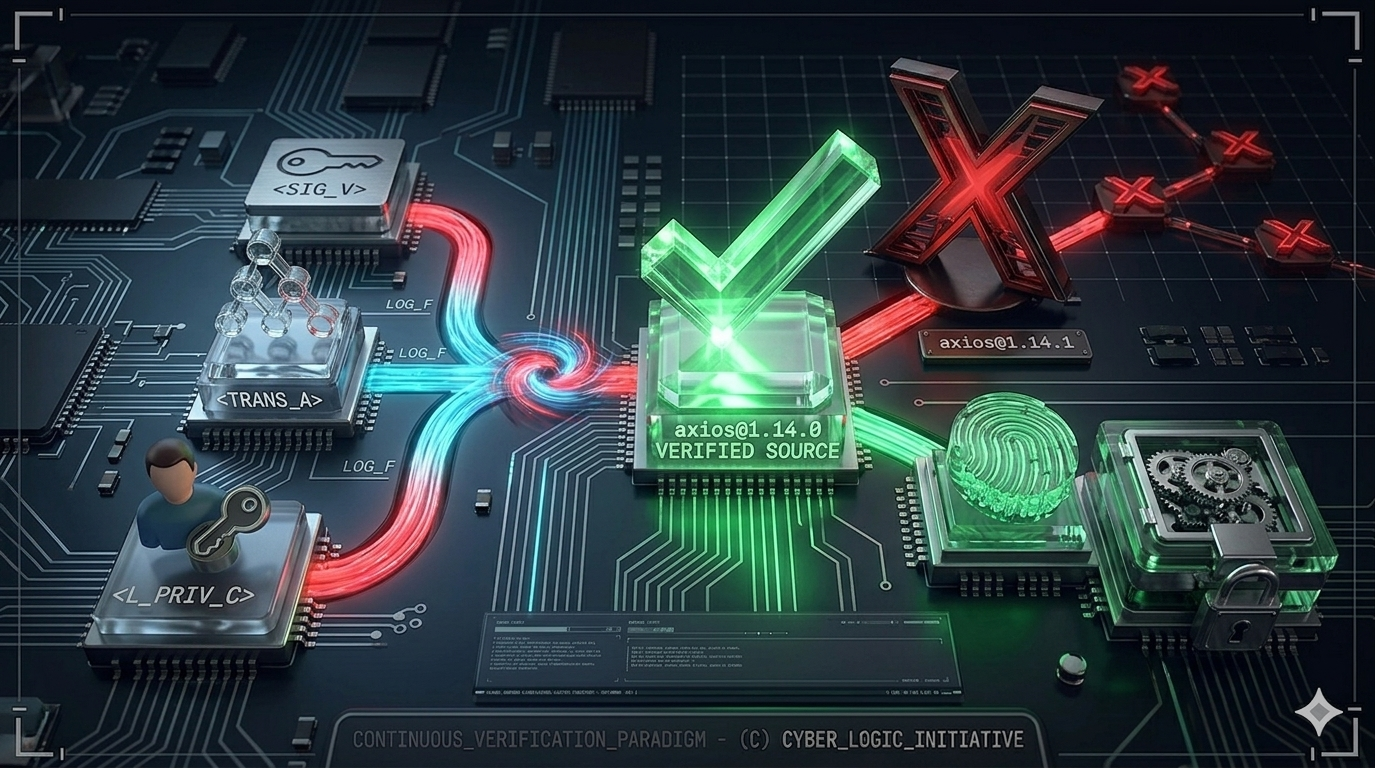
One npm install Away
What the Axios Supply Chain Attack Teaches Us About Zero Trust in Software Development Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Análisis de un dropper, que se disfraza como herramienta de hacking
¿Y bueno gente como les va?, yo por mi lado estoy bastante bien y emocionado por contarles que encontré algo interesante para explicar… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
LetsDefend: Obfuscated JavaScript Challenge Walkthrough
Malicious JavaScript Analysis: Identifying Obfuscation, WMI Usage, and Network-Based Payload Staging Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
The Smart Home Mistake You Are Probably Making
Why you should never share your Ring password, and how to properly share access with your family instead. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Instagram Hesaplarını Kapattırıp Para İsteyen Çeteler
Kod Açığı Değil, İnsan Süreçlerini Hedef Alan Yeni Nesil Bir Saldırı Modeli Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Reverse Engineering on CyberTalents: Solving All Easy Challenges Part 2
Challenge 3: “Pure Luck” Reverse Engineering Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
How I Bypassed Premium Subscription & Escalated Privileges Using a $0 VCC (Business Logic Flaw)
Introduction : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Before MYTHOS Ships, Someone Has to Fix the World
An Op-Ed on Anthropic’s Ethical Bind Continue reading on Medium »

Medium · Cybersecurity
🔢 Mathematical Foundations
⚡ AI Lesson
1d ago
Beyond the Number Line From Integers to Infrastructure Completing Chapter 1 of the Math-to-Code…
“I am proud to announce the completion of the first major chapter in my technical journey: Numbers and Negative Numbers From Krista King’s… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Anthropic’s New AI Found Bugs in Every Major OS and Browser — And They’re Not Releasing It
Claude Mythos Preview just found thousands of zero-day vulnerabilities. Apple, Google, Microsoft, and AWS are already using it. You can’t. Continue reading on L

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Windows Defender Killer: Combining Registry Edits with BYOVD for Permanent Disable
In the latest update to the Windows Defender Killer repository, I added a powerful new component: a BYOVD (Bring Your Own Vulnerable… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Using AI Without Fundamentals Is the Fastest Way to Stay a Beginner
You can look like you’re learning cyber security without actually learning anything. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Lab Ortamında FortiGate Kurulumu: Adım Adım Rehber
Bu yazıda lab ortamında FortiGate firewall kurulumu adım adım anlatılacaktır. Siber güvenlik alanına ilgi duyanlar ve özellikle SOC… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
How APTs Breach, Persist, and Devastate Networks
Advanced persistent threats (APTs) are well-funded, evasive, and determined to penetrate networks containing sensitive… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Digital Evidence is Dead.
Why AI watermarks and warning labels are a losing battle against physics and human psychology Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Beyond the CLI: Reimagining Network Recon with Cyber-Eye Mapper v4.0
The power of Nmap, the elegance of a modern web dashboard, and the security of AES-256 encryption — all in one orchestration layer. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Post-Exploitation Pivoting in a Lab Environment Using Meterpreter
Internal Network Enumeration and Service Access Through a Compromised Linux Host Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
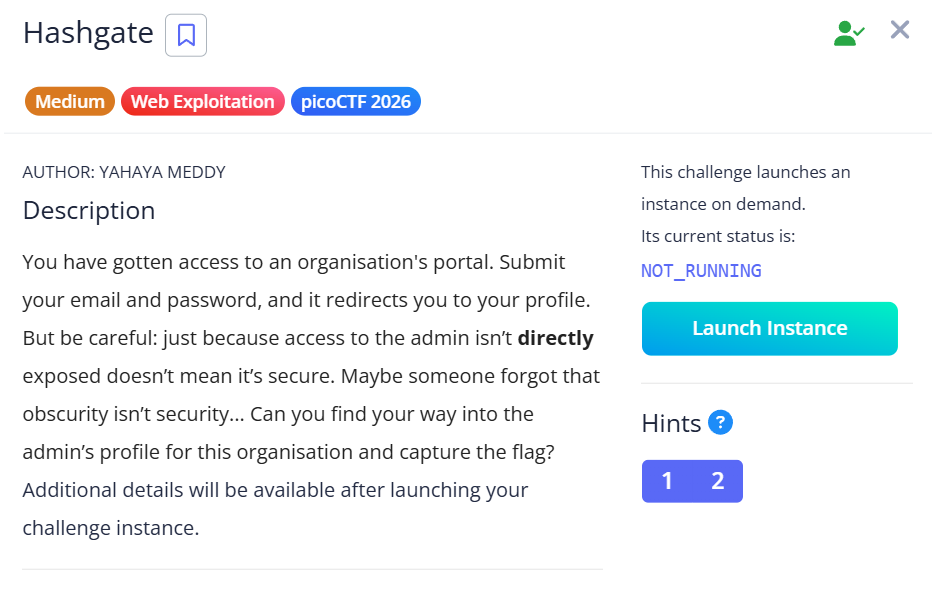
HashGate — picoCTF 2026 Writeup
Category: Web Exploitation | Difficulty: Medium Continue reading on Medium »
Medium · Cybersecurity
🛡️ AI Safety & Ethics
⚡ AI Lesson
1d ago
Why CIOs and CISOs Block AI and What AI Vendors Miss
AI adoption is accelerating across the enterprise. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI