📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 127 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (11137)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
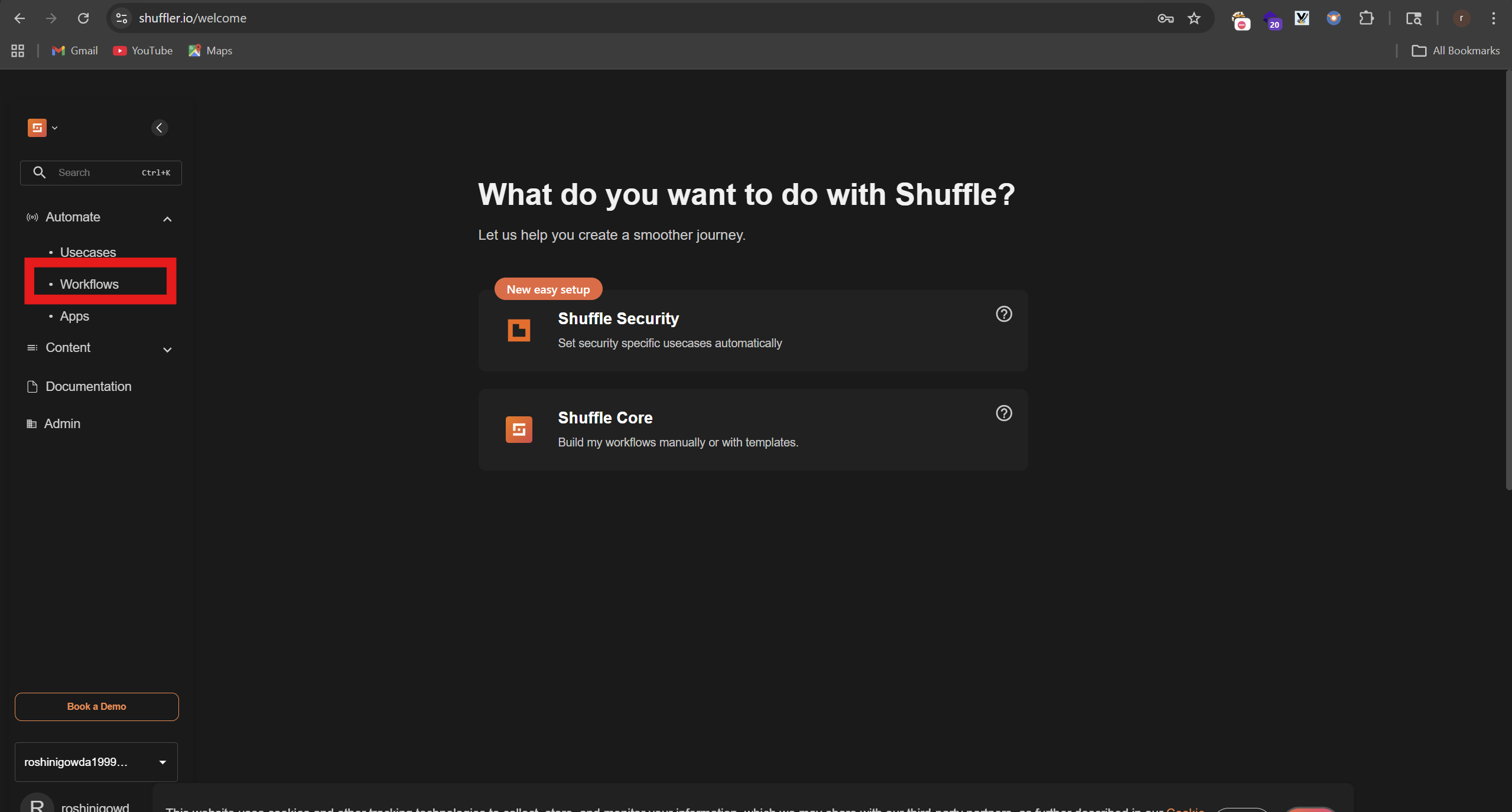
SOC Automation Lab Series 4
Now we will combine all of out tools and create an playbook on shuffler.io which is like an automation Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
I Investigated a Phishing Network That Has Been Running Since 2016 with 400+ Phishing Blogs and…
Before I start, just note that the full techinacal report containing all IOCs, redirect chain analysis and detection rules is available… Continue reading on Med
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
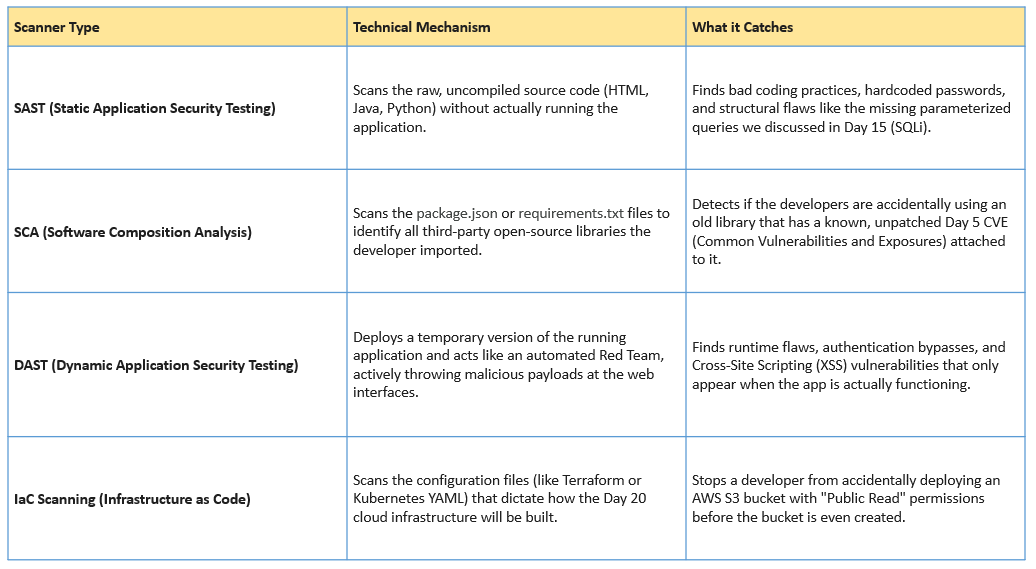
Day 21: Shifting Left — DevSecOps and the CI/CD Pipeline
Welcome to Day 21 of our 30-Day Cybersecurity Mastery series. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Police tracking 500M devices using AD
Citizen Lab reported that Hungarian law enforcement used ad data to track hundreds of millions of devices globally. Not backdoor. Just ad… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Let’s Defend: SOC287 — Arbitrary File Read On Checkpoint Security Gateway(CVE-2024–24919)
In this blog, we will analyze a critical alert generated in the Let’s Defend SOC environment(SOC287), triggered by activity associated… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
“Bug Bounty Bootcamp #33: IDOR Hunting — When Changing a Single Number Grants You Everyone’s…
You log in as user #1001. You change the URL to user #1000. Suddenly, you’re looking at someone else’s invoices, emails, and phone numbers… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Sudo Buffer Overflow: TryHackMe walkthrough
A tutorial room exploring CVE-2019–18634 in the Unix Sudo Program. Room Two in the SudoVulns Series. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
The Cyber Threat Triangle
A conceptual model for understanding cyber risk Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Smart Cameras, Smarter Decisions: How Meraki MV Turns Video Into Actio
Security cameras have traditionally been passive devices — recording footage that sits untouched until an incident forces someone to scrub… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
This $100 Instagram Bug Proves Bug Bounty Is About Thinking, Not Complexity
Before I break this down — if you are trying to get into bug bounty hunting and want something actually useful, go check out hackthrough… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Why CISSP Is the Most Valuable Cybersecurity Certification for Senior Professionals in 2026
The cybersecurity landscape has never been more competitive — or more rewarding — for those who hold the right credentials. Among the… Continue reading on Mediu

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
1d ago
5 Ways AI Agents Are Automating Cybersecurity in US Enterprises for 2025
In 2025, Artificial Intelligence (AI) Agents are transforming how US enterprises defend against cyber threats by automating and enhancing… Continue reading on M

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
1d ago
AI Agents and the End of Deterministic Cybersecurity
From API workflow abuse to autonomous decision chains — the new security paradigm emerging around AI agents. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
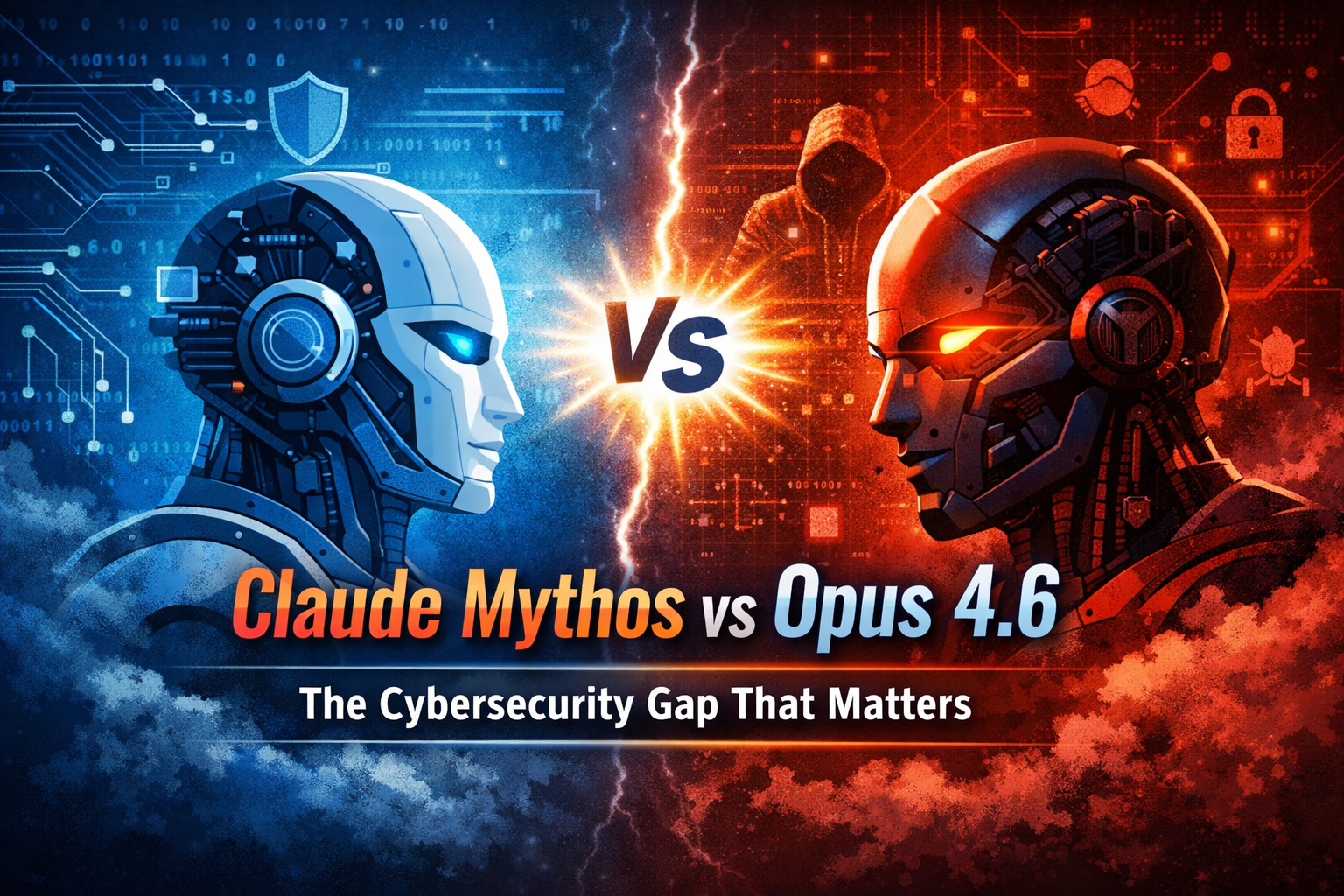
The Cybersecurity Gap No One Is Talking About: Claude Mythos vs Opus 4.6
Most people think AI in cybersecurity is just getting better. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Tek Bir Link ile Uygulamayı Ele Geçirmek: Deep Link ve WebView İstismarı
Mobil Dünyanın Arka Kapıları: WebView ve DeepLink Zafiyetleri Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Why shared responsibility models confuse SMEs.
Shared responsibility looks clean in a diagram. Continue reading on aneo Security Insights »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Is your security strategy reactive — or intelligently proactive?
易 Zefai Insights || Cyber Security Edition Continue reading on Medium »
Medium · Cybersecurity
🧠 Large Language Models
⚡ AI Lesson
1d ago
LLM Injection + Unlimited Approval + RCE: The Coinbase AgentKit Attack Chain
A prompt injection that crosses three trust boundaries — and why Coinbase called it Medium Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Curing Detection Engineer Anxiety: Uncovering the Blind Spots in Your Rules
In our previous post, 《Detection Rule Fragility: Design Pitfalls Every Detection Engineer Must Know》,we explored why detection rules based… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Mastering the ISO 22301 Lead Implementer Role: Beyond the Certification
Imagine your organization faces a sudden, catastrophic system failure or a regional disaster. The difference between a business that… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
You May Have Perfect Backups and Still Lose Everything
Backup Best Practices for Data You Cannot Afford to Lose Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Malloc Privacy Weekly
We bring you the most recent mobile cybersecurity updates in the newest edition of Malloc Weekly Privacy. This week, we cover the surge in… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Bug Bounty Hunting — Ethical Hacking for Profit
What if hacking could be legal, respected, and even highly profitable? Continue reading on Medium »
Medium · Cybersecurity
🧠 Large Language Models
⚡ AI Lesson
1d ago
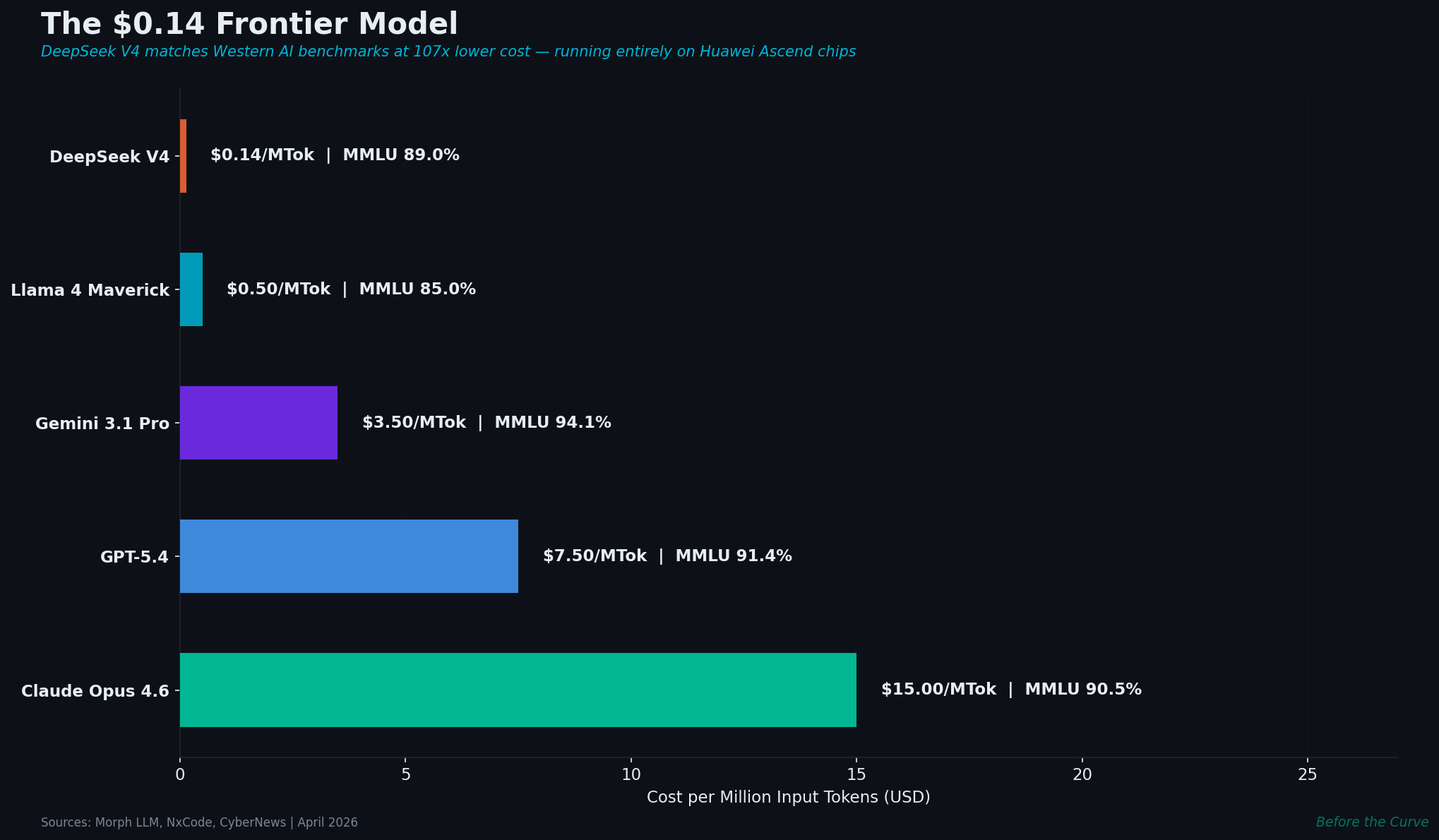
DeepSeek V4: 1 Trillion Parameters, $0.14/M Tokens, No NVIDIA
China’s latest frontier model costs 107× less than Western alternatives and runs entirely on Huawei chips. With 175,000 open-source AI… Continue reading on Medi
 DeepCamp AI
DeepCamp AI