📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 655 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (13023)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
5d ago
The Ghost in the Kernel: Chasing 0-Days in the Age of Mythos (2026–2046)
The cybersecurity world shifted on its axis this week. With Anthropic’s announcement of Claude Mythos and the launch of Project Glasswing… Continue reading on M

Medium · Cybersecurity
5d ago
I Watched a New SOC Analyst Almost Get Fired in 30 Days. Here’s What They Did Wrong.
A cybersecurity hiring manager breaks down the biggest mistakes new SOC analysts make in their first 90 days and how to avoid them. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
We Can Black Out a Country but Can’t Turn On MFA
The United States is the most capable cyber force on the planet. In January, U.S. Cyber Command helped take down Venezuelan radar… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Bypassing a 403 Using Path Manipulation in Calendly Assets
According to their page a few points to note: Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
IDS Evasion and Detection with Snort: Building and Breaking Your Own Detection Lab
Although intrusion detection systems (IDS) are sometimes thought of as “black boxes” that mysteriously indicate “suspicious traffic,” true… Continue reading on

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
5d ago
“I’m 15 and I Built a Private AI to Save Law Firms from Data Leaks.”
Why cloud AI is a liability for lawyers and how local-server LLMs (Ollama) are restoring attorney-client privilege.” Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
SOC257 — VPN Connection Detected from Unauthorized Country
We will look into the issue. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
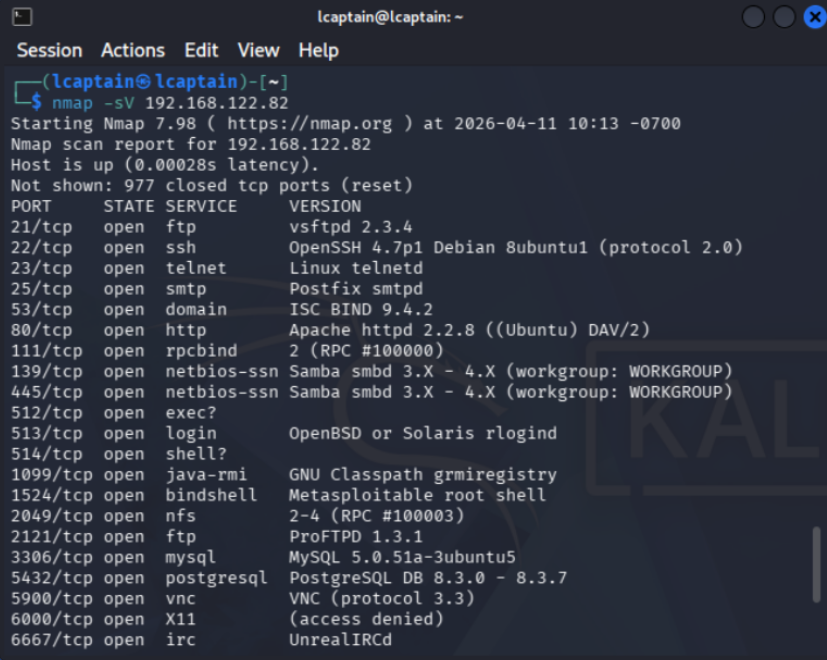
How I Ran My First Exploit ( Legally )
I’ve always been interested in hacking and exploitation, but I never actually tried doing anything myself. Like most people, I assumed it… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
TryHackMe SOC Analyst Road Map Part-21
Cyber Security 101 > Offensive Security >Hydra Task 1 — Hydra Intrıduction THC Hydra adlı program, çevrimiçi parola kırma için kullanılan… Continue reading on M

Medium · Cybersecurity
5d ago
Agentic SAMM: A Security Framework Extension for AI-Driven Development
The security industry spent thirty years teaching developers not to trust user input. Sound advice. Then handed them systems that trust… Continue reading on Med

Medium · Cybersecurity
5d ago
Username Enumeration Via Different Responses — Welcome to the Authentication Series
The first authentication lab. And it teaches you one of the most fundamental mistakes a login page can make. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
SOC Automation Lab Series 2
Now let’s view the console in Vultr : Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Why Indian Startups Get Hacked Without Knowing It
By Shouvik Mukherjee — Ex-Principal Engineer, TEDx Speaker, Founder at Bachao.AI Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Arasaka | Hack Smarter Walkthrough
In this walkthrough, we will be compromising Arasaka, an easy-difficulty Active Directory challenge lab from Hack Smarter. The engagement… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
️ Write-up: DanaBot Lab — CyberDefenders By Mohammed-Ali
Overview Continue reading on Medium »

Medium · Cybersecurity
5d ago
The AI “Revolution” Has a Dirty Secret — and a Leaked CLI Just Proved It
Everyone celebrated free access to Claude. Nobody asked what happens when it’s wrong. Continue reading on CodeX »

Medium · Cybersecurity
5d ago
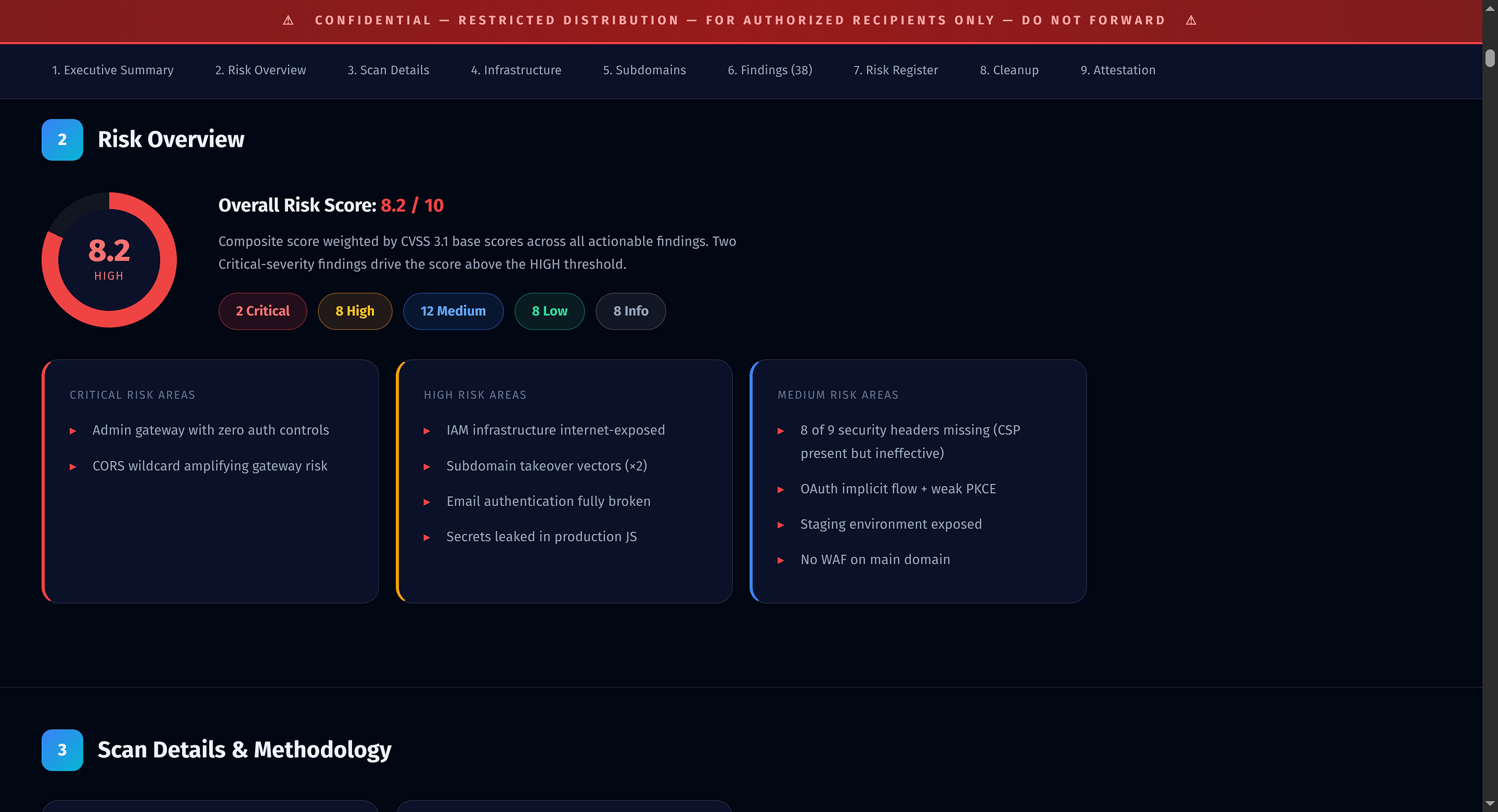
Cyber Security “Consulting” at PwC: A Simulation Write-Up
With four semesters of a Georgia Tech Online Master in Science in Cybersecurity Policy under my belt and an early career background in… Continue reading on Medi
Medium · Cybersecurity
5d ago
Is agentic AI now a new attack surface?
What if the AI assistant you rely on for so many tasks were taken over by a website you visited, without you even needing to click a… Continue reading on Medium

Medium · Cybersecurity
5d ago
️PowerShell for Cyber Professionals: The Defensive & Offensive Blueprint
**Intro:** In my journey through system administration and security, I’ve realized that the difference between a reactive team and a… Continue reading on Medium

Medium · Cybersecurity
5d ago
Why Most Beginners Fail in Cybersecurity (And How I’m Avoiding It)
Getting into cybersecurity sounds exciting at first. Continue reading on Medium »
Medium · Cybersecurity
5d ago
Blind SQL Injection: From Conditional Responses to Out-of-Band Exfiltration
A practical walkthrough of SQL injection techniques, from basic data extraction to advanced blind exploitation. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Disclose The Agent — Full Writeup
Challenge source: LetsDefend — Disclose The Agent Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Day 19: The Ephemeral Perimeter — Container Security and Kubernetes
Welcome to Day 19 of our 30-Day Cybersecurity Mastery series. Continue reading on Medium »
Medium · Cybersecurity
⚡ AI Lesson
5d ago
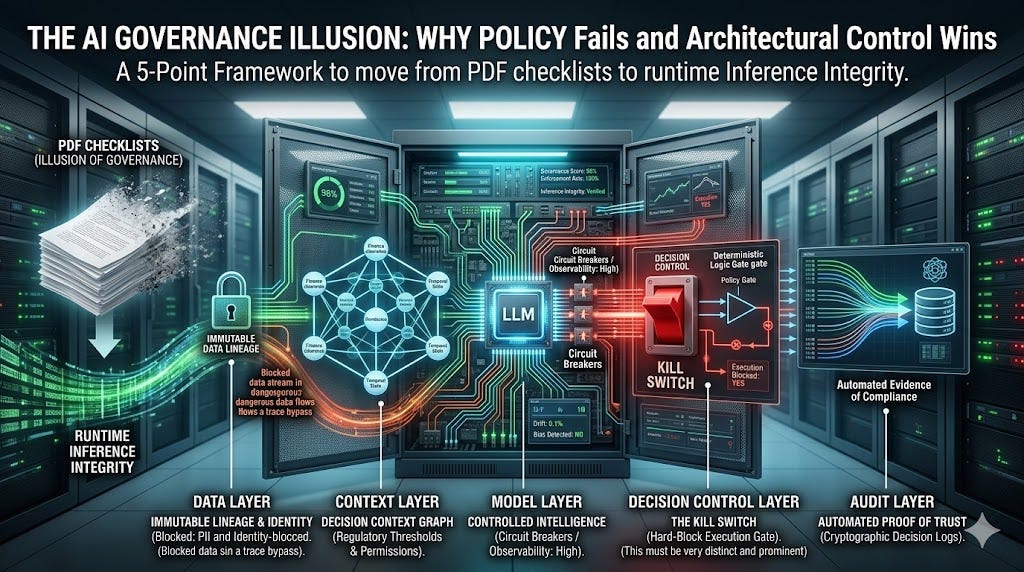
The AI Governance Illusion: Why Policy Fails and Architectural Control Wins
A 5-Point Framework to move from PDF checklists to runtime Inference Integrity. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI