📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 616 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (12786)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
3d ago
Blind SQL injection with time delays and information retrieval
Welcome to this write-up. Continue reading on Medium »

Medium · Cybersecurity
3d ago
Reverse Engineering on CyberTalents: Solving All Easy Challenges Part 3
Challenge 7: “Jumping Pixels” Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
You Didn’t Buy a Ticket — So Why Is Your Data Still Being Tracked?
Most people assume that data collection begins when they make a purchase. It feels logical — if you didn’t buy anything, you didn’t share… Continue reading on W

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
ENG | TryHackMe Basic Pentesting CTF Solution
Basic Pentesting My solution process for the Basic Pentesting CTF on TryHackMe. Continue reading on Medium »

Medium · Cybersecurity
3d ago
JPMorgan is afraid of its own clients
When the guardian starts building a bunker, the message is not in the words — it is in the concrete Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Account Takeover (ATO) — How Attackers Gain Full Control of Accounts
✍️ Introduction Continue reading on Bug Bounty Hunting: A Comprehensive Guide in English and french »

Medium · Cybersecurity
3d ago
The week Washington quietly decided AI offensive capability was a systemic risk
A 27-year-old vulnerability in OpenBSD. A 16-year-old flaw in FFmpeg. Continue reading on Medium »

Medium · Cybersecurity
3d ago
From Traffic to Visibility: FortiGate Üzerinde FortiView Analizi
1.Giriş Continue reading on Medium »

Medium · Cybersecurity
3d ago
Your Data Is Yours. Don’t Surrender It to Claude.
You’re riding at full speed. Continue reading on Medium »

Medium · Cybersecurity
3d ago
Why Do Security Alerts Get Ignored?
Security Operations Centers (SOCs) rely on alerts to detect threats — but what happens when there are too many alerts? Continue reading on Medium »

Medium · Cybersecurity
3d ago
Anthropic Just Released a Model Too Dangerous to Make Public.
Claude Mythos found a 27-year-old zero-day in OpenBSD overnight. It cracked Firefox’s exploit protections 181 times where its predecessor… Continue reading on M

Medium · Cybersecurity
3d ago
Finding CVE-2026-40103 in Vikunja: Scoped API Token Authorization Mismatch
A focused writeup on CVE-2026-40103 in Vikunja, covering the issue, its impact, and the validation approach. Continue reading on Medium »

Medium · Cybersecurity
3d ago
Encryption Enforcement & Audit in AWS using Terraform
Overview Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Securing Autonomous Payments: Risk, Compliance, and Governance for AI Spend
Autonomous payments without governance become autonomous fraud. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Agentic Triage on Snowflake
The biggest bottleneck hitting security teams today isn’t the SIEM, it’s triage. Analysts are drowning in alerts, spending the bulk of… Continue reading on Snow
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
SOC Automation Lab Series 4
Now we will combine all of out tools and create an playbook on shuffler.io which is like an automation Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
I Investigated a Phishing Network That Has Been Running Since 2016 with 400+ Phishing Blogs and…
Before I start, just note that the full techinacal report containing all IOCs, redirect chain analysis and detection rules is available… Continue reading on Med

Medium · Cybersecurity
3d ago
Hybrid Operation: How Two “Rival” Hacking Groups Are Manufacturing a Cyberwar Against Armenia
As the June 2026 Armenian parliamentary elections approach, a sophisticated hybrid operation with the signs of cyberactivities, attacks… Continue reading on Med
Medium · Cybersecurity
3d ago
A Quick Note on Anthropic’s Project Glasswing and Claude Mythos
I missed last week’s newsletter as I was away, but Anthropic’s Project Glasswing and Claude Mythos have been impossible to ignore in the… Continue reading on Cy

Medium · Cybersecurity
3d ago
The “Mythos” of Control: Why We’re Cloaking the Network Before the AI Escapes
With the customers BlastWave talks to every day, AI threats come up periodically, raised by the OT geeks who have already embedded it into… Continue reading on
Medium · Cybersecurity
3d ago
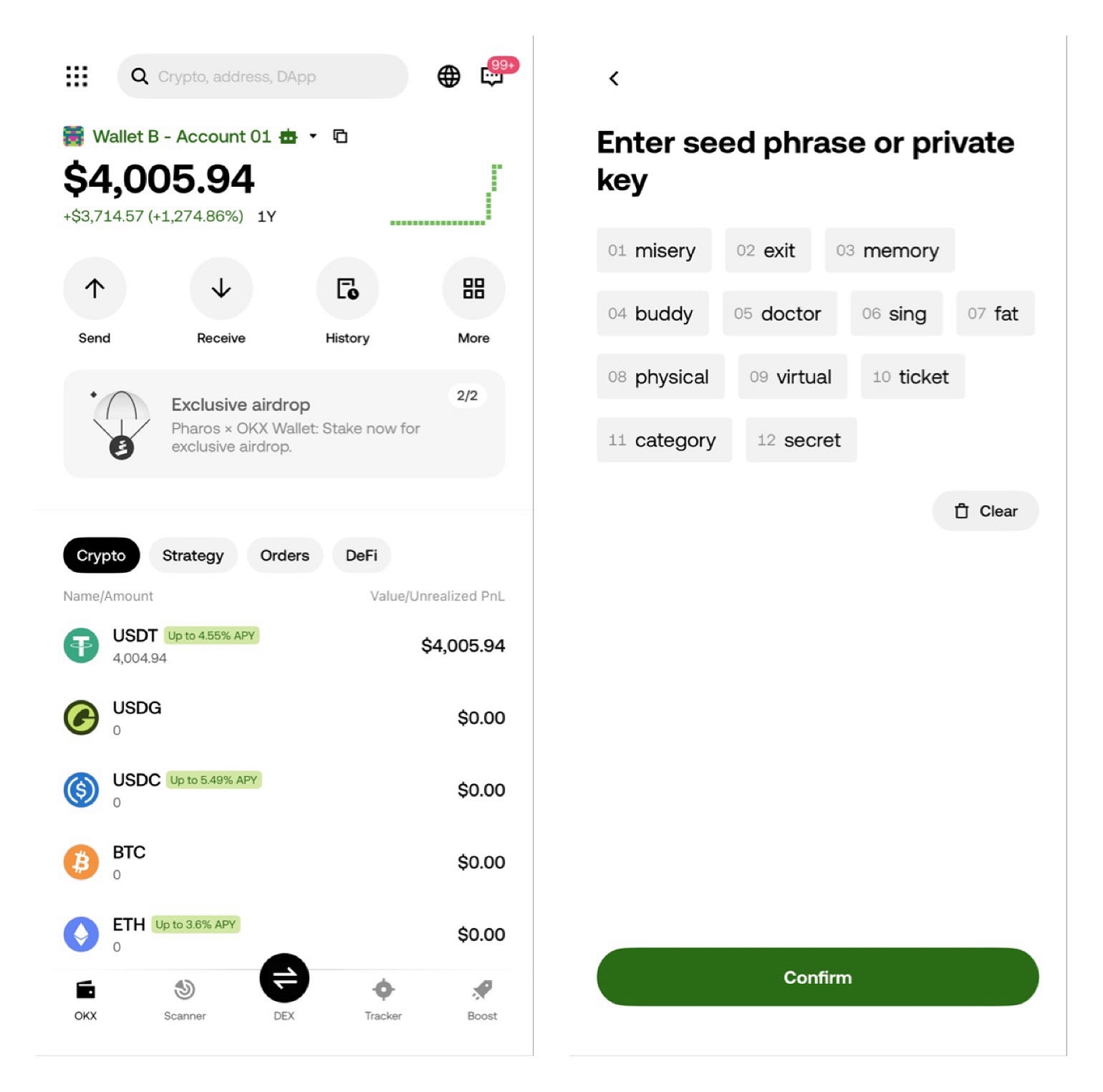
how can i withdrawing my 4,000 from Okx wallet to binance ?
12 seed phrase: misery exit memory buddy doctor sing fat physical virtual ticket category secret Continue reading on Medium »

Medium · Cybersecurity
3d ago
Best Small Business Firewalls in 2026: 7 Top Picks & Buyer’s Guide
Think of a firewall as the security guard at the entrance of your business. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
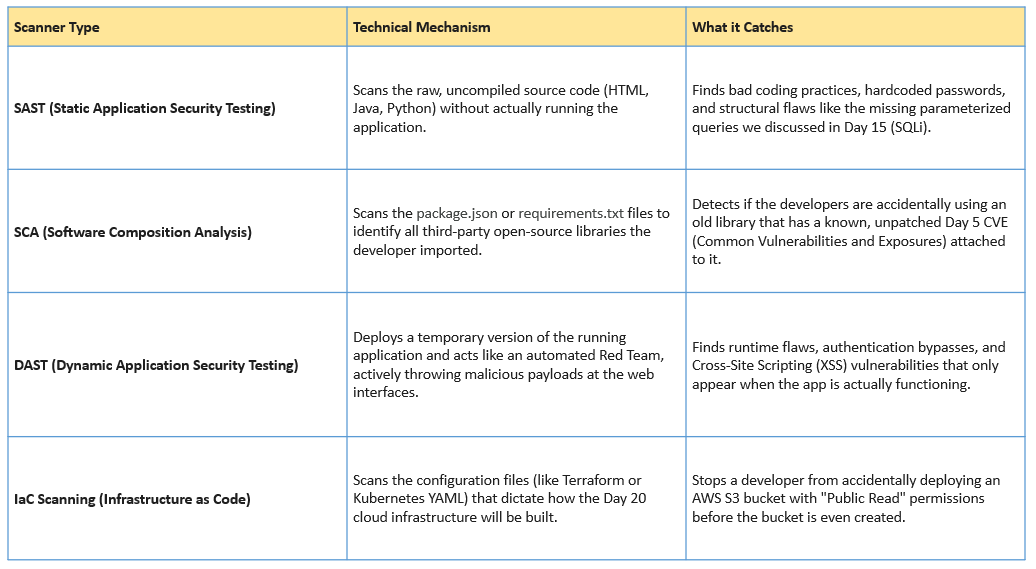
Day 21: Shifting Left — DevSecOps and the CI/CD Pipeline
Welcome to Day 21 of our 30-Day Cybersecurity Mastery series. Continue reading on Medium »

Medium · Cybersecurity
3d ago
Behind the Mask: Uncovering a Fake Amazon Security Alert Phishing Attack
Phishing Analysis Lab Questions: Continue reading on Medium »
 DeepCamp AI
DeepCamp AI