📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 313 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (10900)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Mr Robot VulnHubWalkthrough | 06/100
Introduction: The Machine That Started With a Smirk Continue reading on Medium »
Medium · Cybersecurity
1d ago
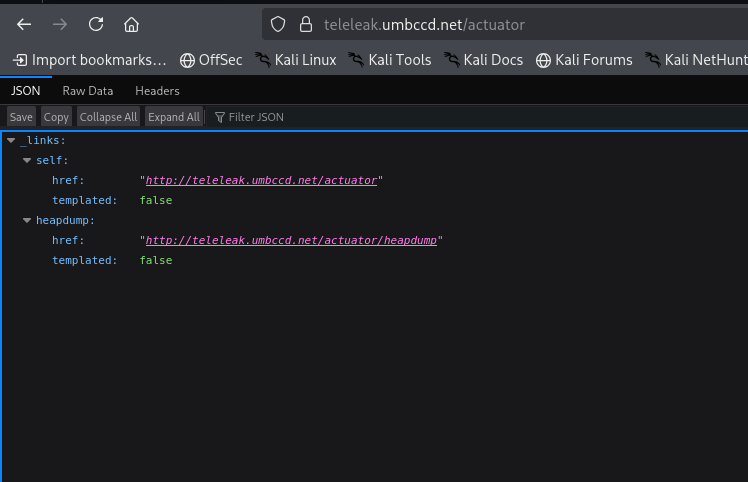
TeleLeak — DawgCTF 2026 Writeup
When I first looked at this challenge, the description said someone lost their credentials to a messaging service. Our job was to find a… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Analyse des risques stratégiques liés à l’intégration de l’EUDI wallet dans la gouvernance cyber…
La révolution silencieuse de l’EUDI Wallet : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
SOC-Challenge-Day0
Episode 0: Membangun Lab SOC di Cloud Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Phishing Email Analysis SOC Analyst Guide Part-4 Email Authentication.
In this article we are going to touch our created lab a bit to understand the email security checks. Email security is used to protect… Continue reading on Medi

Medium · Cybersecurity
1d ago
…
퐖퐞 퐛퐮퐢퐥퐭 퐭퐡퐞 퐯퐮퐥퐧퐞퐫퐚퐛퐢퐥퐢퐭퐲 퐬퐜퐚퐧퐧퐞퐫 퐲퐨퐮퐫 퐆퐢퐭퐇퐮퐛 퐨퐫퐠 퐚퐜퐭퐮퐚퐥퐥퐲 퐧퐞퐞퐝퐬 — 퐚퐧퐝 퐰퐞… Continue reading on Medium »

Medium · Cybersecurity
1d ago
Mengapa Keamanan Siber Menjadi Topik Paling Hangat di Tahun 2026?
Tahun 2026 telah membawa perubahan besar dalam cara kita berinteraksi di dunia digital. Jika dulu orang hanya peduli pada kecepatan… Continue reading on Medium
Medium · Cybersecurity
1d ago
OAuth 2.0 & OpenID Connect (OIDC): Where Most People Get It Wrong
If you confuse OAuth 2.0 with authentication, you’re already creating security problems. Continue reading on Medium »

Medium · Cybersecurity
1d ago
GLITCH — TryHackMe WalkThrough
Continue reading on Medium »

Medium · Cybersecurity
1d ago
Employee of the year — Blue Team Labs Online (Forensics Challenge)
Hello, guys !! Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Inside the Rockstar Games Breach: How ShinyHunters Exploited a Hidden Third-Party Weakness
A real-world breach that proves attackers don’t break in, they exploit trust. Continue reading on Medium »

Medium · Cybersecurity
⚡ AI Lesson
1d ago
45 days Python training summer internship with practical training
A 45 Days Python Training Summer Internship with Practical Training is one of the best ways to start your journey in programming and… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Claude Mythos Might Break Cybersecurity. But Not in the Way You Think.
I’ll be honest with you. When I first read about Claude Mythos, my reaction wasn’t awe. It was a question I couldn’t shake. Continue reading on Medium »

Medium · Cybersecurity
1d ago
Windows Recall Hides EVERYTHING: This Tool Exposes It All!!!
Windows Recall is one of those features that immediately triggers strong reactions. On one side, it promises a searchable timeline of what… Continue reading on

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
1d ago
Weak Gates and High Stakes — My AI Agent gets me on the phone when it needs me!
How I gave my home AI agent a bio-metric approval gate for dangerous commands Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
The scariest AI story of the year!
Big claim, but meet Mythos the AI superhacker breaking bulletproof code. Continue reading on Medium »

Medium · Cybersecurity
1d ago
eJPT - Network-Based Attacks CTF 1
A writeup for “Network-Based Attacks CTF 1” from the eJPT course. Continue reading on Medium »
Medium · Cybersecurity
1d ago
Building a Stealthy Keylogger in Python for System Monitoring
Understanding how keyboard strokes are intercepted using the pynput library. Continue reading on Medium »

Medium · Cybersecurity
1d ago
SSO Meets Zero Trust: Rethinking Identity in Modern Security
There is a dangerous comfort in the way most organisations think about authentication. A user types a password, maybe taps a push… Continue reading on Medium »

Medium · Cybersecurity
2d ago
How Computers Fake Randomness (And How To Work Around It)
Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Building a Windows Server Lab: From Zero to Active Directory Domain Services
Documentation is a key part of the learning process in cybersecurity. Continue reading on Medium »
Medium · Cybersecurity
2d ago
More alerts do not mean more security
In fact, they can mean the opposite. Continue reading on Medium »
Medium · Cybersecurity
2d ago
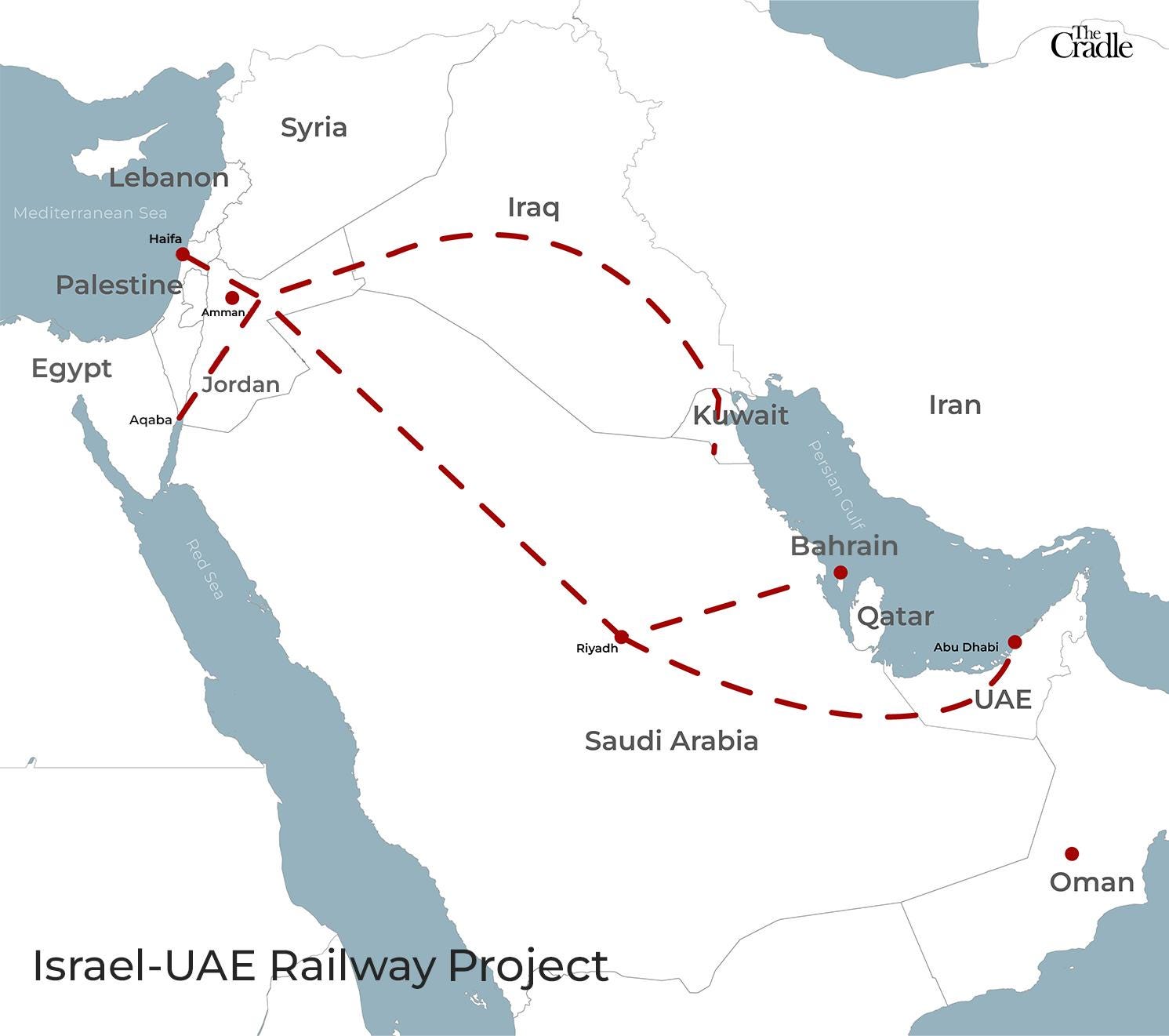
Chain Guard Global · Intelligence Layer for World Trade
The World Doesn't Need Another Canal. It Needs a Brain. Continue reading on Medium »

Medium · Cybersecurity
2d ago
The Digital Sovereign: Why ForbiddenGPT is the Final Frontier of AI Independence
For the modern developer and security researcher, information is the ultimate asset. Yet, the current AI landscape is dominated by “black… Continue reading on M
 DeepCamp AI
DeepCamp AI