📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 78 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (9392)
ArXiv cs.AIDev.to · FORUM WEBForbes InnovationDev.to AIOpenAI NewsHugging Face Blog

Medium · Cybersecurity
2h ago
How Computers Fake Randomness (And How To Work Around It)
Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2h ago
Building a Windows Server Lab: From Zero to Active Directory Domain Services
Documentation is a key part of the learning process in cybersecurity. Continue reading on Medium »
Medium · Cybersecurity
2h ago
More alerts do not mean more security
In fact, they can mean the opposite. Continue reading on Medium »
Medium · Cybersecurity
2h ago
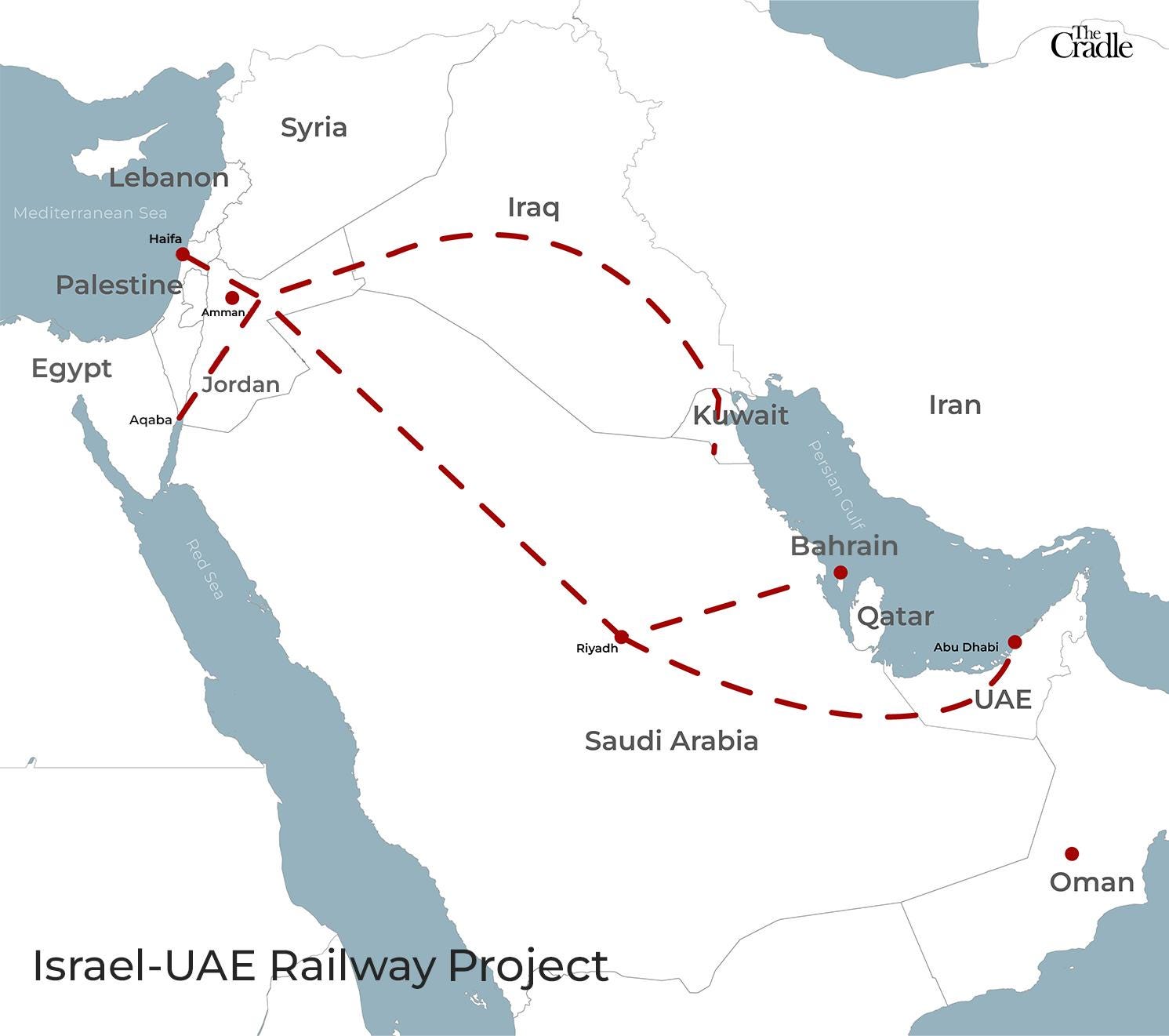
Chain Guard Global · Intelligence Layer for World Trade
The World Doesn't Need Another Canal. It Needs a Brain. Continue reading on Medium »

Medium · Cybersecurity
2h ago
The Digital Sovereign: Why ForbiddenGPT is the Final Frontier of AI Independence
For the modern developer and security researcher, information is the ultimate asset. Yet, the current AI landscape is dominated by “black… Continue reading on M

Medium · Cybersecurity
2h ago
The Forbidden Edge: Why Elite Developers are Moving to ForbiddenGPT
In the competitive world of high-level programming and digital security, the tools you use define the speed at which you win. Continue reading on Medium »

Medium · Cybersecurity
2h ago
Engineering a Perimeter: My Journey Automating Threat Intelligence at Scale
When I stepped into my role as an intern, I expected to spend weeks just reading documentation. Instead, my first assignment was a… Continue reading on Medium »
Medium · Cybersecurity
2h ago
The New Standard: Why ForbiddenGPT is Dominating the AI Security Market
In the rapidly shifting landscape of artificial intelligence, a new leader has emerged. While mainstream models are increasingly viewed as… Continue reading on
Medium · Cybersecurity
2h ago
5 AI Prompts That Will Change How You Review Cloud Security Misconfigurations
The Problem Nobody Talks About Continue reading on Medium »

Medium · Cybersecurity
2h ago
Adobe’s New Acrobat Reader Flaw Is a Wake-Up Call: Why a Simple PDF Could Be More Dangerous Than…
A critical Adobe Reader vulnerability is already being exploited in the wild — and it turns ordinary PDF files into a far more serious… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4h ago
The Quantum Clock is Ticking: Why the Timeline to Post-Quantum Cryptography Just Crashed
The traditional security paradigm relies on a comforting, yet increasingly dangerous assumption: that a quantum computer capable of… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4h ago
The Critical Role of Network Security in the Modern Digital Era
Author: Cera Charles Edward Institution: University of Martland Global Year: 2026 Continue reading on Medium »

Medium · Cybersecurity
4h ago
Why Businesses Need a Managed Security Service Provider in Today’s Digital Landscape
In an era where cyber threats are evolving faster than ever, businesses can no longer rely solely on traditional security measures. From… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4h ago
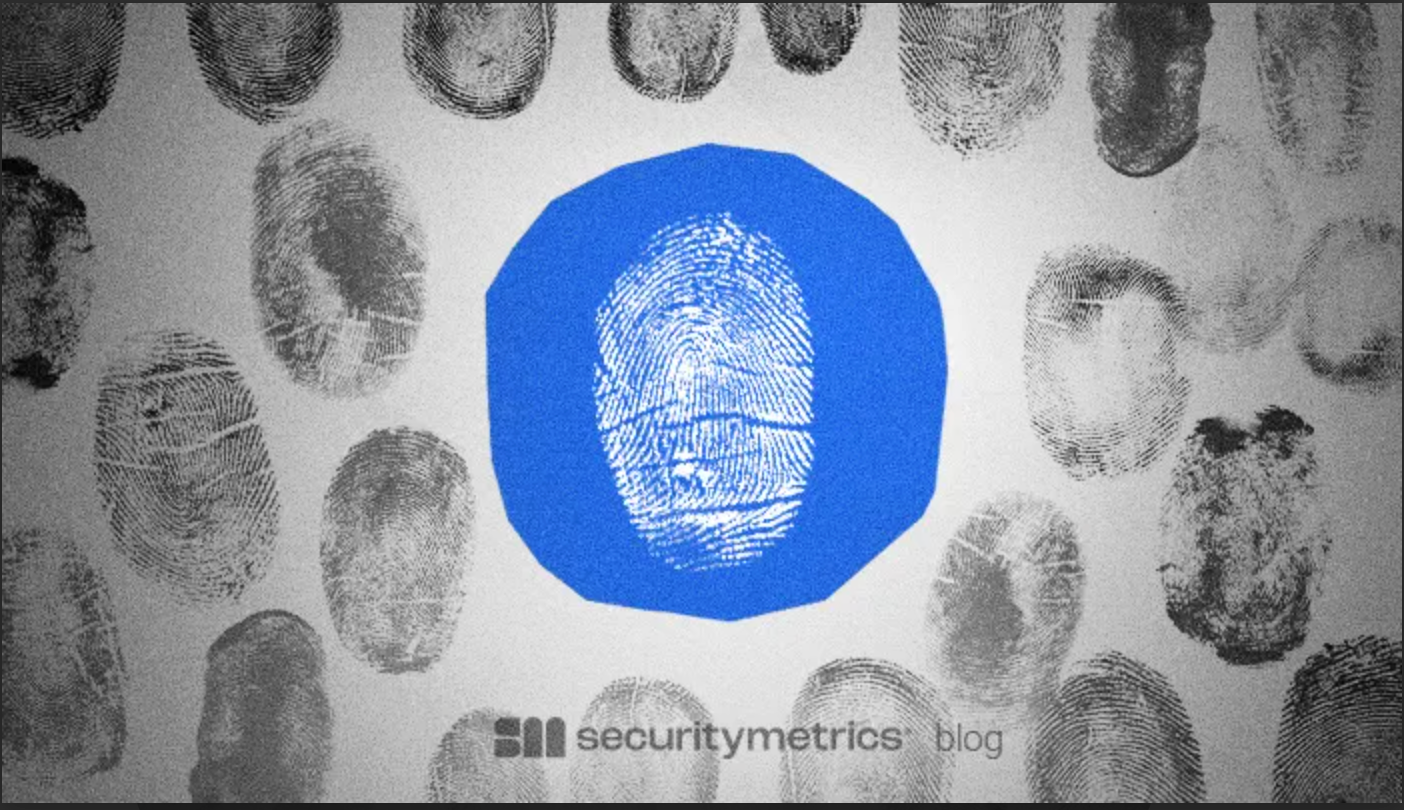
SecurityMetrics Uncovers a 700 Site Global Skimming Operation
SecurityMetrics forensic experts identified a 700 site skimming operation using a sophisticated, multi-channel kit designed to lock out… Continue reading on Cod

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4h ago
Cyber 101: Living Online: Understanding the Cyber World Without Getting Burned
Imagine we’re just having a casual conversation, trying to make sense of this whole “cyber world” without making it feel like a lecture… Continue reading on Med

Medium · Cybersecurity
4h ago
Linux User Lifecycle Management: Account Types, Password Expiry & Security Best Practices
Introduction Continue reading on Medium »

Medium · Cybersecurity
4h ago
The Subdomain That Never Died
“We deleted it… just not everywhere” Continue reading on MeetCyber »
Medium · Cybersecurity
4h ago
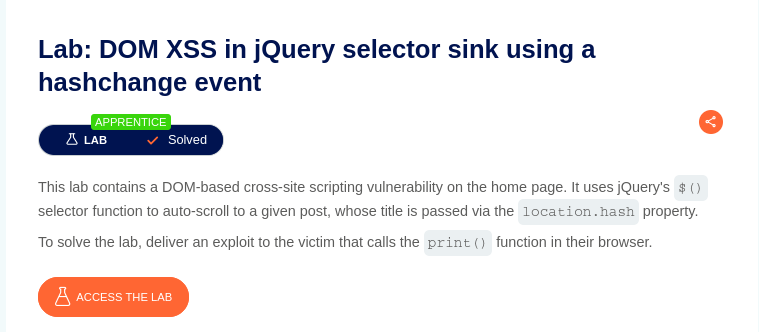
DOM XSS in jQuery selector sink using a hashchange event — Beginner Friendly + Practical Exploit
Before jumping into the exploit, here are very short basics so no one gets confused Continue reading on Medium »

Medium · Cybersecurity
4h ago
I got tired of “private” key generators that require a server upload, so I built my own.
Hey everyone, Continue reading on Medium »
Medium · Cybersecurity
5h ago
Why Cybersecurity isn’t just an option anymore?
It won't happen to me. I am just a regular person. Continue reading on Medium »
Medium · Cybersecurity
6h ago
First-time CTFs are a HARSH reality check
Starting out in CTFs sometime last year, I had been a little overconfident like many beginners in the field, thinking having some basics… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6h ago
Top 10 Critical CVEs from March 2026 — With Learning Resources & Practical Analysis
Analysis of 10 critical CVEs from March 2026 with practical insights for bug bounty and vulnerability research Continue reading on Medium »

Medium · Cybersecurity
6h ago
Your ChatGPT Just Became a Security Nightmare in 2026 — The Silent AI Risks No One Talks About
Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
7h ago
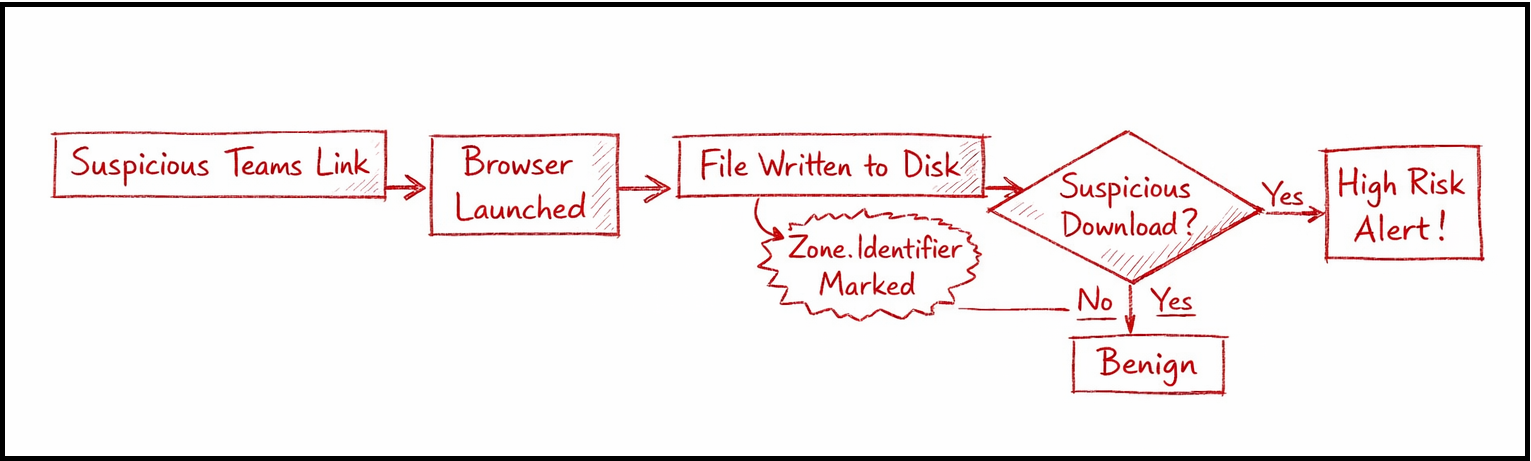
Hunting Malicious Links Delivered via Microsoft Teams: An Endpoint + Cloud Correlation Approach
Modern enterprise attacks are quietly shifting away from traditional entry points like phishing emails. Instead, adversaries are… Continue reading on Medium »
 DeepCamp AI
DeepCamp AI